Sniffers go by many names, including packet sniffers, packet analyzers, network probes, wireless sniffers, and Ethernet sniffers. “Sniffer” with a capital S refers to the trademarked tool by NetScout, which allows network administrators to monitor bandwidth and make sure no single user is taking up too much capacity. With a lowercase s, “sniffer” refers to all other types of packet sniffers, both benign and malignant.
While sniffers aren't actually viruses, they can be packaged with malware and used by hackers to spy on your online activity, recording everything you’re doing, including your usernames and passwords, credit card details, and other private information.
What is network sniffing software used for?
Sniffers were originally designed to be used by professional network engineers and system administrators to monitor traffic and ensure their networks stayed safe. Unfortunately, today’s hackers can take advantage of sniffing software that’s available online.
Legal sniffer uses
Most legitimate sniffers are used to maintain the smooth flow of traffic through a network. Here are some of the many legal ways network sniffers are used by cybersecurity professionals, system administrators, and network engineers:
-
To ensure smooth traffic flows
-
To capture data packets traveling through a network
-
To record and analyze traffic
-
For firewall testing
-
For packet decryption
-
For network troubleshooting
-
To detecting malware or hacking activity
How do hackers use sniffers?
Hackers use sniffer software to capture, decode, and analyze packets of data sent over a network using TCP/IP or other protocols. Using packet sniffing tools, hackers can spy on people and steal their personal data, usually with the goal of identity theft or another form of fraud.
Hackers use sniffers to:
-
Capture private info like usernames, passwords, credit card numbers, etc.
-
Record communications such as emails and instant messages
-
Commit identity fraud
-
Commit financial fraud
How does a sniffer work?
Sniffers work by capturing internet traffic and analyzing the data streams to uncover the nature — or even the specific contents — of data sent across a network.
Just as cars make up road traffic, internet traffic consists of packets of data traveling through a network. Although you generally ignore most cars driving by, you’re likely to investigate if a truck pulls up in your driveway. Similarly, your computer ignores most traffic flowing through a network, and only inspects the specific packets of data that are sent to it.
Sniffers, then, are like a tollbooth — they are set up to inspect all cars driving down the road, not just those that park in one driveway. Unfiltered sniffers inspect every car, harvesting all traffic traveling through a network. Filtered sniffers are configured to inspect only certain types of traffic.
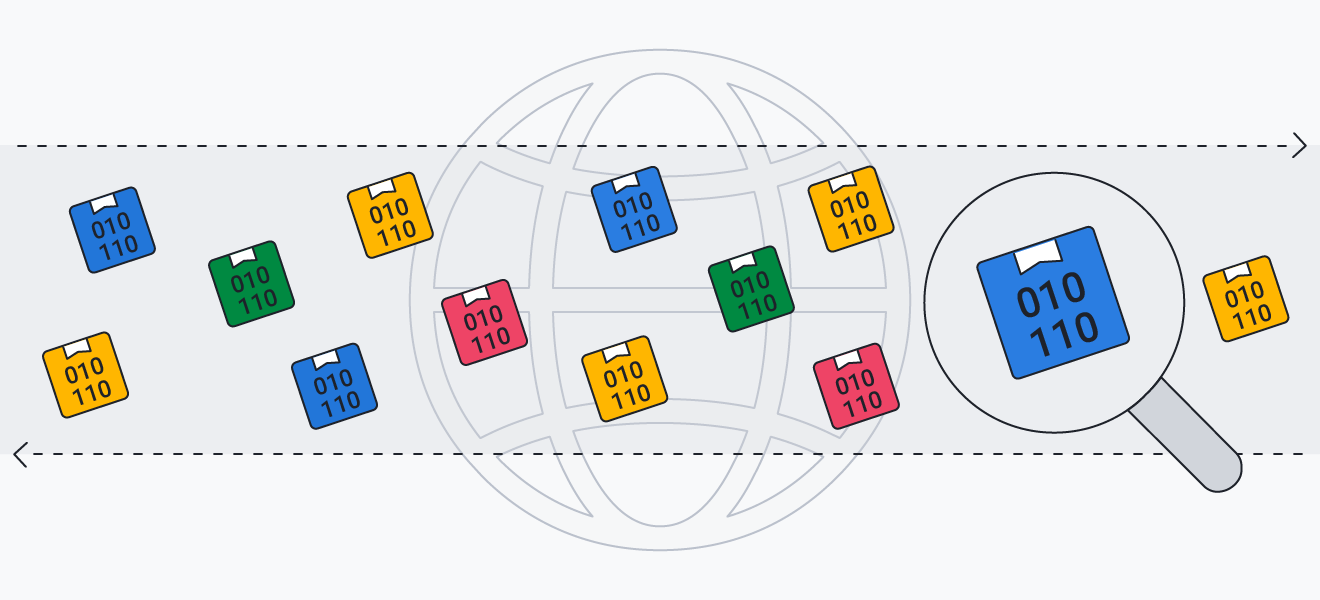 Packet sniffers capture and analyze the data packets that flow through a network.
Packet sniffers capture and analyze the data packets that flow through a network.
Software sniffers vs. hardware sniffers
Sniffers can come in the form of software or hardware. Network or system admins can sniff on traffic using hardware like routers with built-in sniffing capabilities. Sniffing hardware consists of a special adapter that hooks into the existing network. The adapter collects the data and either stores it or sends it along to a collector for further inspection.
Hackers, for their part, tend to use sniffing software. Normally, computers ignore all traffic that’s headed elsewhere on a network, but sniffing software applications essentially alter a computer’s settings and permissions so that it collects and copies all available data packets on the network. That lets the hacker store all the network data and analyze it later. This kind of sniffing is referred to as promiscuous mode, and it’s just about as shady and unrestricted as it sounds.
Although there's no such thing as a sniffer website, you may encounter sniffers by visiting unsafe sites that automatically download sniffer apps. Or, you can get caught in a phishing scam that includes infected attachments or links. Another way to become a victim of sniffing is by using unsecured Wi-FI networks.
Passive vs. active sniffing
There are two types of sniffing: active and passive. Passive sniffing can capture traffic without directly interacting with it. But some networks require a more active approach to sniffing that involves disrupting traffic protocols to intercept data.
If your network is structured using hubs — which connect several devices together on one network — then all the traffic flows freely. That means your computer actually receives all the traffic in the network, but it ignores everything that isn’t addressed to it. A sniffer can passively peek in, and instead of ignoring irrelevant traffic, it absorbs it all. This type of passive sniffing is quite difficult to detect.
On larger networks, it’s not possible for all traffic to reach all devices, so network switches are used to point traffic only to the specific device it’s addressed to. For a hacker to successfully sniff in this type of environment, they’d have to bypass the constraints enforced by the switches, which constitutes active sniffing. This is generally done by spoofing the network with additional traffic, and it means that active sniffing is generally easier to detect than passive sniffing.
What information can be found by a packet sniffer?
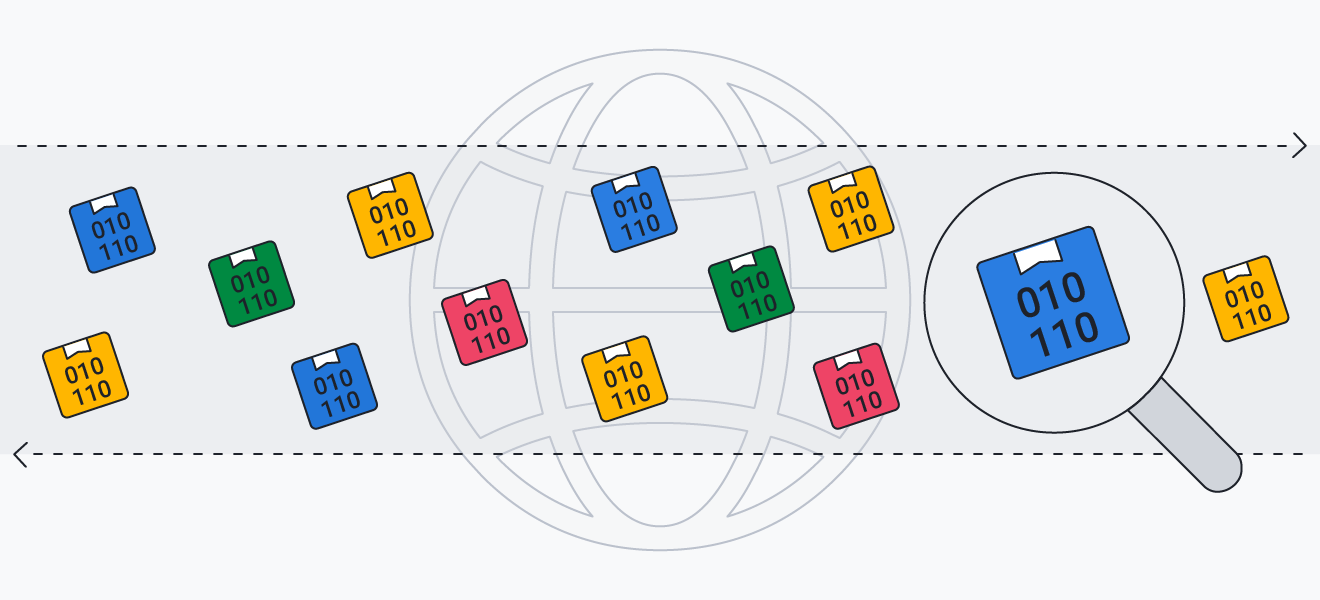
Packet sniffers can be used to collect practically any data or communications shared over a network. A packet sniffer can record your passwords and login credentials, see which sites you visit and what you do there, and uncover your IP address and physical location. Companies use sniffers to monitor activity on their networks and scan traffic for malware.
Unlike other, less intrusive forms of snooping — such as ad tracking — there are almost no limits to the type of information that can be intercepted and captured by a packet sniffer, which is why they can be such dangerous tools in the wrong hands.
 Packet sniffers can collect almost any data or communications shared over a network.
Packet sniffers can collect almost any data or communications shared over a network.
Examples of packet sniffers
There are a variety of free or cheap sniffing tools available online. Most of them are marketed for the purpose of helping you learn about capturing and analyzing network traffic to troubleshoot issues. Solutions like Wireshark and CloudShark are presented for only legitimate uses. Others, such as the cheekily named BUTTsniffer, are more transparent about their possibly nefarious applications.
By following our prevention tips below, you should avoid encountering any sniffers in the wild.
How to protect your system from a sniffer
As the saying goes, an ounce of prevention is worth a pound of cure, and this definitely applies when it comes to network sniffers. Here’s how to prevent sniffer attacks:
-
Use strong antivirus software: A robust antivirus will prevent malware from invading your system. It will also detect anything that shouldn’t be on your computer — like a sniffer — and help you delete it. AVG AntiVirus FREE has the protection you need and will help you both remove and prevent malware.
-
Avoid public Wi-Fi: Open Wi-Fi networks, like those found in coffee shops or airports, are often unsafe networks. Although there are ways to browse more safely on public Wi-Fi, it can be easy for hackers to sniff the entire network. You should avoid using them without a VPN.
-
Use a VPN: A Virtual Private Network secures all the data sent from your computer over the internet by encrypting your connection and hiding your IP address. Using a robust VPN like AVG Secure VPN means that a sniffer spying on your traffic would just see scrambled info, while your data stays safe.
-
Avoid unsecured protocols: Check for the HTTPS protocol (often indicated by a lock icon) on the address bar of the websites you visit. That means that the site is secure and your web traffic is encrypted. You should avoid unsecured protocols like HTTP when possible, especially when banking or shopping online.
-
Watch out for social engineering: Cybercriminals use methods like spear-phishing emails and infected websites to trick victims into compromising their own security and unwittingly downloading sniffers. Practice smart browsing tactics and common sense to avoid anything fishy.
How to find a sniffer on your network
Passive sniffers can be difficult to detect. And while active sniffing is a bit more visible, you’re still going to need some amount of tech savviness. If you think someone might be sniffing on your traffic, you could run your own sniffer and monitor all the DNS traffic in your network to detect any suspicious activity.
In theory, even the most stealthy passive sniffers can be uncovered if you really know what you’re doing. But you’ll need to have administrator privileges and the know-how to figure out if any interfaces have been configured in “promiscuous mode” (such as via the ifconfig command in Linux).
An easier and better solution is to rely on the above steps detailing how to prevent packet sniffing, especially by using top-rated antivirus software and a virtual private network (VPN) to encrypt your connection.
How to remove a sniffer
If a sniffer gets on your device, you need to remove the malicious software immediately to protect your privacy. You can do this manually by checking all of the apps on your computer and uninstalling any that look suspicious or that you don’t remember downloading. But you may find a sniffing app that can’t be uninstalled.
In that case, you’ll need to use a strong anti-malware tool such as AVG AntiVirus FREE, which will scan and remove malicious software. It also has special defenses against infected downloads, unsafe links, and harmful email attachments, which will further prevent sniffers and other viruses from infecting your device. Get AVG today to block online threats and keep your personal data private.

 Packet sniffers capture and analyze the data packets that flow through a network.
Packet sniffers capture and analyze the data packets that flow through a network. Packet sniffers can collect almost any data or communications shared over a network.
Packet sniffers can collect almost any data or communications shared over a network.




