What is pretexting?
Pretexting is a social engineering ploy by which scammers fabricate plausible stories — or pretexts — to lure victims into giving up personal information or account access. Such schemes present a false, yet believable scenario to gain the victim's trust and make them feel comfortable revealing certain information.
The element of the pretexting definition that sets it aside from other forms of social engineering is the highly detailed or specific story — the pretext — the scammer creates. This helps manipulate the victim into accepting the scammer's story and sharing sensitive data such as account passwords, social security numbers, and even credit card details.
Pretexting attack — social engineering techniques
Unlike other cyber-threats, pretexting attacks don’t rely on computer hacking or other technical methods to breach systems. Instead, pretexting scammers take advantage of people's trust and trick them into compromising their own security by freely divulging private information.
Pretexting tactics usually involve a scammer playing a convincing character that’s used to develop a fake, but plausible, story that the victim can relate to. These stories tap into a victim’s emotions and suspend any suspicions they may have.
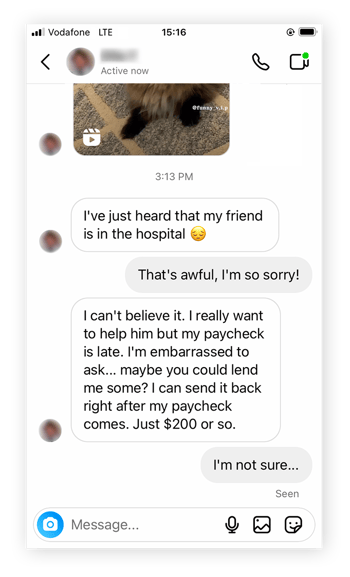 Pretexting scams can use social engineering tactics to take advantage of a victim’s emotions.
Pretexting scams can use social engineering tactics to take advantage of a victim’s emotions.
Because this kind of social engineering attack relies entirely on a victim's belief in the pretexting story — and willingness to comply with the attacker’s requests — when planning a pretexting attack, fraudsters usually seek to target victims that are:
-
Trusting
-
Vulnerable
-
Influential
-
Ignorant of threats
-
Not tech-savvy
-
Respectful of authority
Depending on who they’re targeting, and what kind of data they’re after, scammers leverage an entire playbook of pretexting tactics. Let’s take a look at some of the specific techniques that may be used as part of a pretexting scam
Phishing
The vast majority of pretexting scams involve phishing attacks designed to trick people into revealing personal information or clicking on a link that may lead to a malware infection. But unlike regular phishing ploys, social engineering pretexting often uses a more focused spear phishing attack as a way of initiating and sustaining a connection over a longer period of time.
 Phishing attacks try to trick people into clicking malicious links.
Phishing attacks try to trick people into clicking malicious links.
For example, a pretexting scenario might be established by a phishing email inviting you to a surprise party for someone you vaguely know, such as a colleague from another department. This might then be followed up by another email about contributing toward a gift. Finally, an SMS arrives with a seemingly legit payment link to steal your money.
Vishing and smishing
Phishing has grown into such a big cyber security problem that vishing — voice phishing — has been categorized as its own subgroup. Likewise, smishing, or SMS phishing, happens when a predator tries to lure you into a scheme using text messages.
If smishing is used as part of a pretexting scheme, the SMS might be something simple and seemingly harmless to set the stage for a larger attack. Social engineering pretexting often carries an elaborate backstory so incorporating smishing as part of a pretexting cyber security attack is common.
Tailgating and piggybacking
Pretexting schemes that involve physical access to a building or facility often use tailgating or piggybacking to do so. While tailgating involves sneaking into a building behind an authorized individual, piggybacking relies more on social engineering than stealth.
A “piggybacking” threat actor tells a believable story to an authorized individual and convinces them to let them inside the facility. Tactics include lying about having forgotten their access badge or even posing as a delivery courier.
Whaling
If phishing reels in small fish, whaling catches the biggest creatures in the sea. Whaling is a type of pretexting tactic that grooms high-profile employees as part of a larger company attack. Even executives are susceptible to spear phishing and whaling attacks, because they are based on social engineering, which plays to human weakness and vulnerabilities.
 Whaling attacks target high-profile people.
Whaling attacks target high-profile people.
Impersonation
Pretexting often involves impersonation of an official employee, utility worker, or someone who is assumed to have a right or need to access sensitive information. Such impersonation doesn’t necessarily need to be particularly sophisticated, because people tend to be naturally deferential and trusting of people in positions of authority, or those acting in an official capacity.
An all-too-common example of this kind of pretexting attacks is a tech support scam, which involves a scammer pretending to be a representative of a large, well-known company in order to gain remote access to your device, lure you into clicking a malicious link, or trick you into making bogus payments.
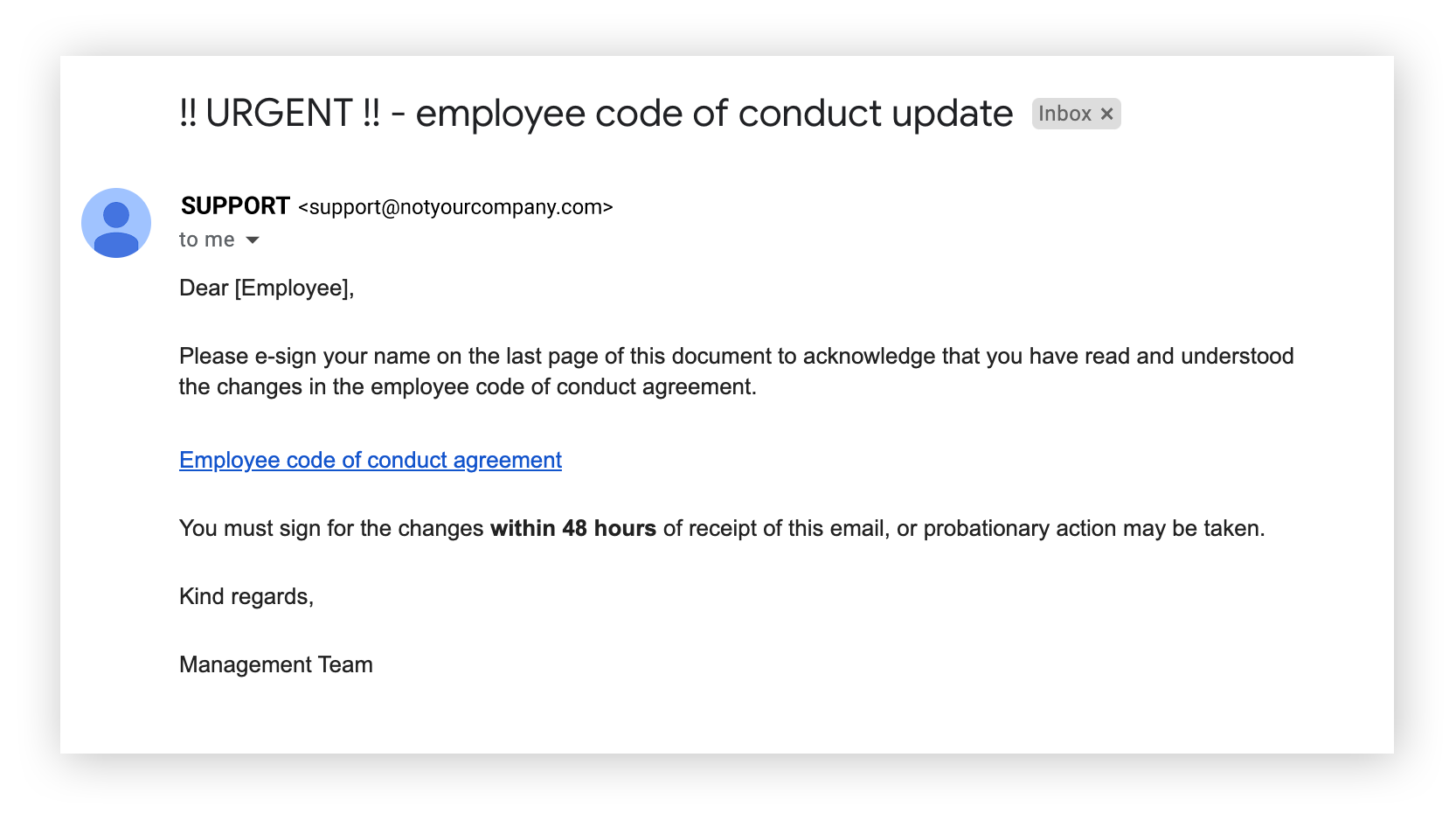
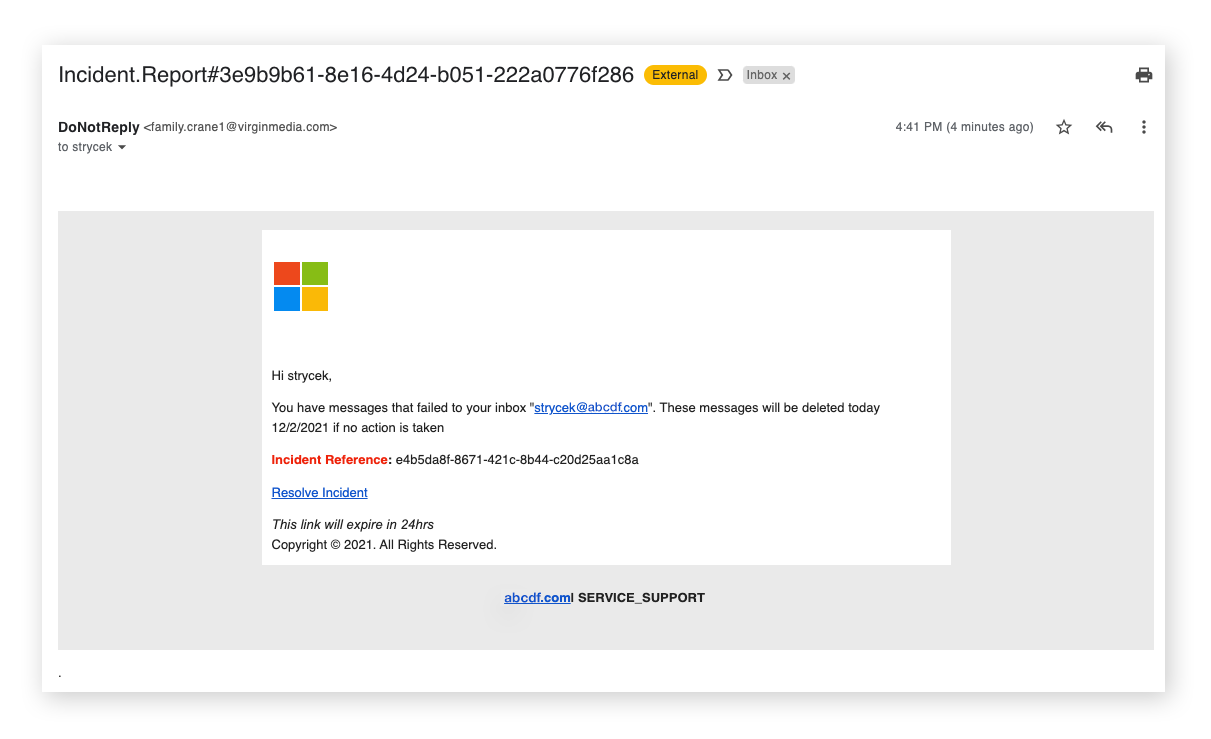 Check that communications you receive from brands are legit.
Check that communications you receive from brands are legit.
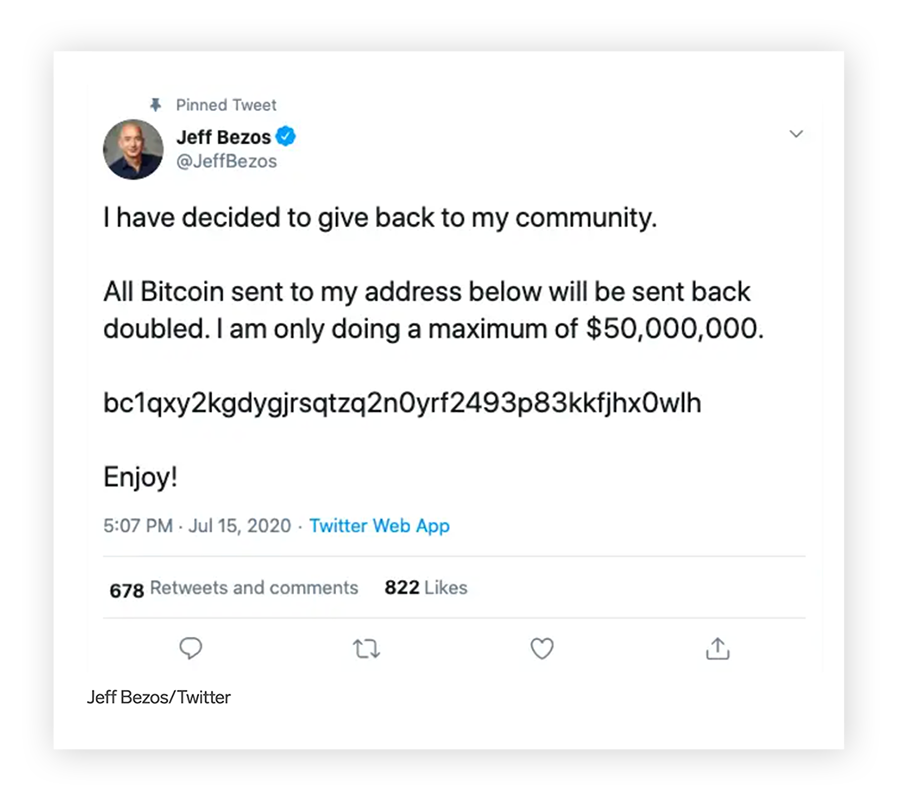
Baiting
Baiting is designed to lure a victim into taking action with the false promise of a reward such as a phony refund or cash prize. If used in a pretexting scheme, the scammer will create a scenario designed to make the victim feel confident and secure in taking the bait. This might include spoofing, to make it appear that communications are from a trusted contact or organization.
Scareware
Scareware is a type of malware that bombards you with alarming messages of threats and dire consequences if you don't take immediate action like downloading fake virus software. By inducing a sense of panic, scareware can cause victims to act irrationally and make poor decisions that they normally wouldn't.
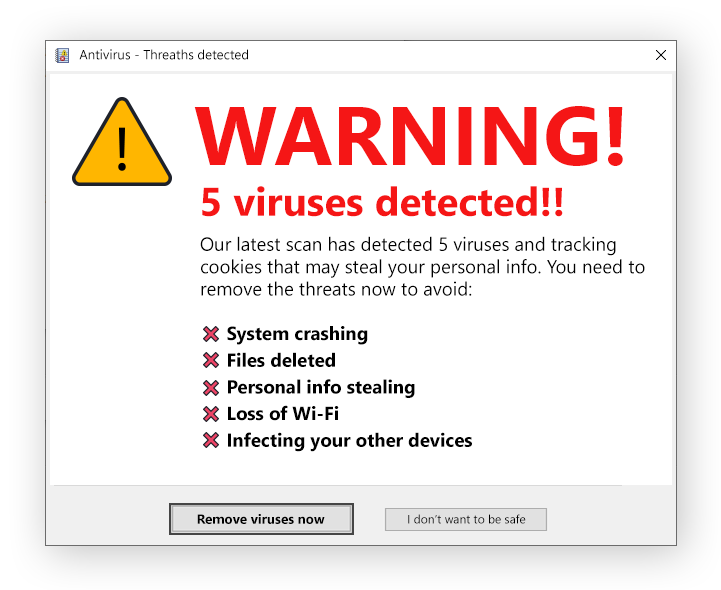 Scareware tries to convince you that you have malware on your device.
Scareware tries to convince you that you have malware on your device.
Common examples of a pretexting attack
Real life pretexting examples include numerous hacking attacks on notable companies and high-profile individuals, as well as the hundreds of thousands of regular folks who are targeted every year. The most common types of pretexting scams include:
-
Gift card scams
Scams with gift cards often begin with an SMS or email that asks you to click a link or provide contact details to claim a prize.
-
Internet service provider ploys
Fake ISP schemes involve imposters pretending to be your ISP to try to convince you to reveal sensitive information.
-
Subject line requests
These pretexting attacks come through emails with catchy subject lines pretending to be from a trusted source.
-
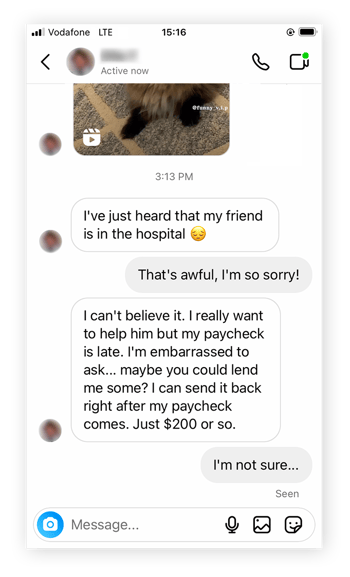
Grandparent scams
Family pretexting attacks involve urgent requests to wire money to support a family member apparently in dire need.
-
Romance scams
Romance scams happen when scammers trick you into a fake online relationship that seems to have potential for a real life romance. Often the fraudster asks for financial support (this is also known as catfishing).
-
Venmo scams
Online payment scams, like Venmo scams, happen when scammers trick you into sending them money through the popular payment app.
Given the range of different approaches, personas, and scenarios scammers concoct to hoodwink their victims, there are practically endless variations of each type of pretexting attack, which is why it’s often so difficult for victims to detect and avoid this type of fraud.
Pretexting attacks can also be astonishingly sophisticated, and span several years before getting exposed, as was the case when a pretexting scammer swindled $100 million from Google and Facebook by sending a series of fake invoices between 2013 and 2015.
What is the difference between phishing and pretexting?
Although phishing and pretexting may seem very similar, phishing is an attack medium, while pretexting is an attack method. The two can overlap, such as in a highly targeted spear-phishing email impersonating a target’s friend, relative, or employer. But although many pretexting attacks use phishing communications as part of their scheme, not all pretexting scams involve a phishing component.
How to recognize pretexting attacks?
Pretexting attacks are, by design, difficult to recognize, but there are a number of tell-tale signs that may indicate that something’s not quite as it seems. Here are some red flags to watch out for that can help alert you to this kind of scam:
-
Urgent language: In order to complete their attacks quickly, pretexters may try to create a sense of urgency by using language like “ASAP,” “immediately,” or "right away."
-
Strange requests: Be wary of any request that requires sensitive information, the transfer of funds, or unusual downloads, even if it follows normal communication channels and conversation styles.
-
False familiarity: Be suspicious of messages with casual openings like "Are you free right now?" or "Can you do me a favor?" that come out of the blue — even if they’re purportedly from someone you know.
-
Avoiding ongoing communication: Pretexters often come up with various excuses to avoid ongoing communication, and they make the victim reluctant to question or verify the scammer’s requests.
-
Spoofed domains: Attackers imitating a legitimate website may use similar email or URL domains, potentially including easy-to-miss spelling errors or discrepancies in the sender's email or linked URL.
Often, by the time you’ve identified a pretexting scam, the phishing or hacking attack has already gone too far and a data breach has already happened. Nevertheless, you should always report internet scams and take the necessary steps to secure your compromised accounts and devices, which helps to prevent identity theft.
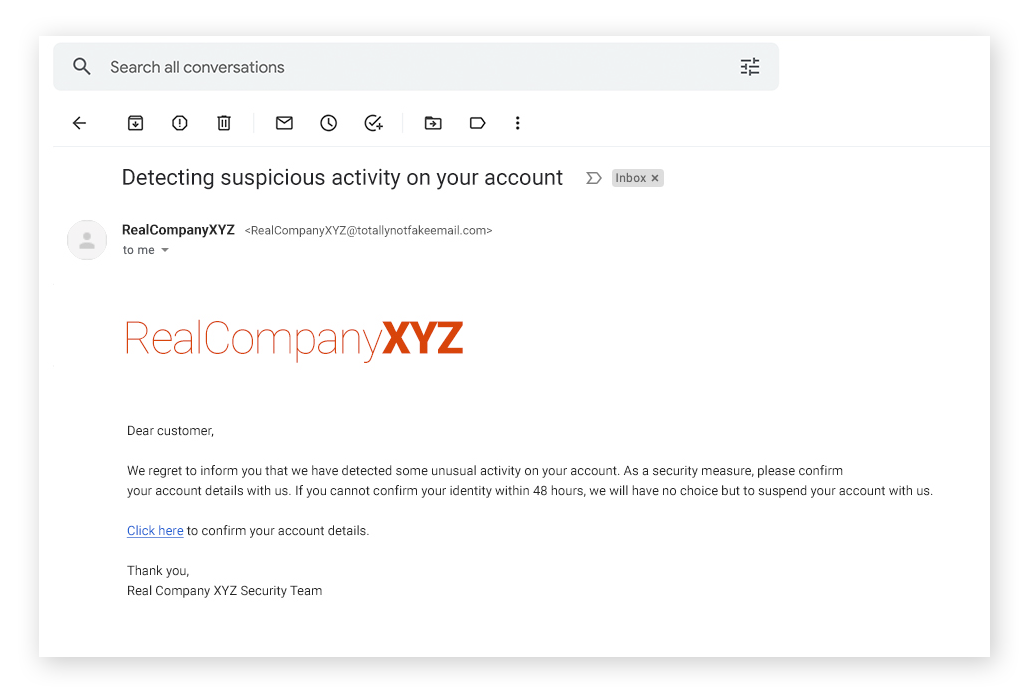 Signs of a spoofing email include fake email addresses, suspicious links, and missing or fake contact information.
Signs of a spoofing email include fake email addresses, suspicious links, and missing or fake contact information.
How to prevent pretexting attacks
The most valuable step an organization or individual can take to prevent pretexting is to educate themselves on email security and common pretexting tactics. Knowing how pretexting works and what to look out for helps you avoid becoming victim.
Follow these steps to help prevent pretexting scams targeting you and your data:
-
Be vigilant for red flags like urgent language, spoofed email addresses, or suspicious requests.
-
Don't click on any unverified links or download suspicious attachments.
-
Don't share sensitive information with anyone before verifying their identity.
-
Contact the sender through a verified channel to authenticate their request.
-
Report suspicious correspondence to your supervisors and IT professionals.
-
Report the fraud to your local authorities — if you’re in the US, report fraud to the FTC.
Pretexting law in the US
Any form of pretexting with fraudulent intent is illegal in the US. Not only is it prohibited to impersonate authorities, such as law enforcement, the Telephone Records and Privacy Protection Act of 2006, which protects records kept by telecommunication companies, further establishes smishing, vishing, and other pretexting attacks as crimes.
Additionally, the Gramm-Leach-Bliley Act makes it illegal to obtain or try to obtain, disclose or try to disclose, customer information of a financial institution when acquired using fraud or deception. This makes the vast majority of security pretexting for personal banking data illegal.
Help prevent pretexting attacks with AVG
No matter how savvy and discerning you are, sophisticated social engineering techniques can be very convincing. AVG AntiVirus FREE helps you identify scams before they unfold, thanks to automatic threat detection that helps block phishing links, alert you to fake websites, shut down scareware, and quarantine malware in real time. Stop pretexting scammers from accessing your data. Install AVG today — completely free.

 Pretexting scams can use social engineering tactics to take advantage of a victim’s emotions.
Pretexting scams can use social engineering tactics to take advantage of a victim’s emotions.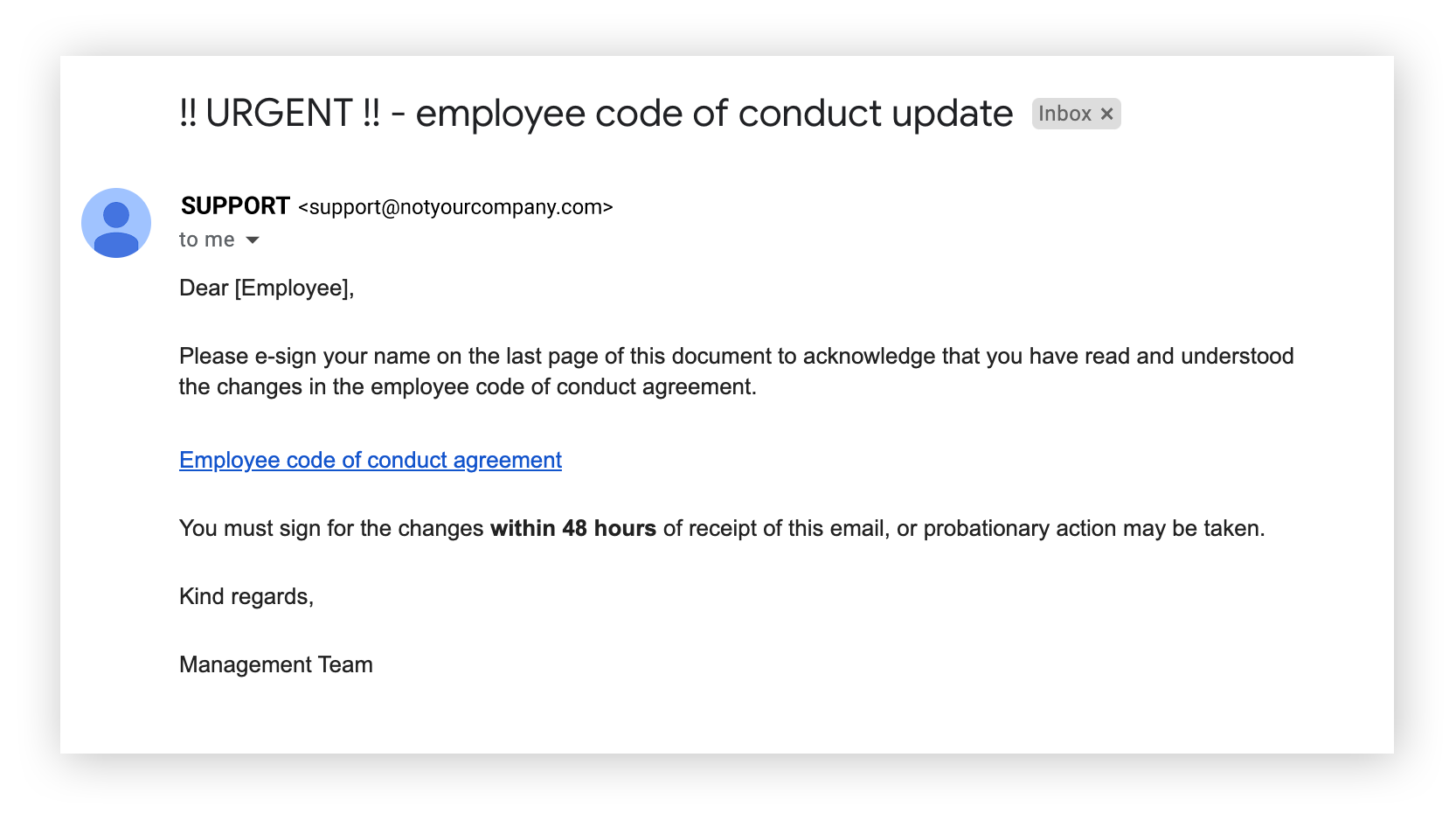 Phishing attacks try to trick people into clicking malicious links.
Phishing attacks try to trick people into clicking malicious links.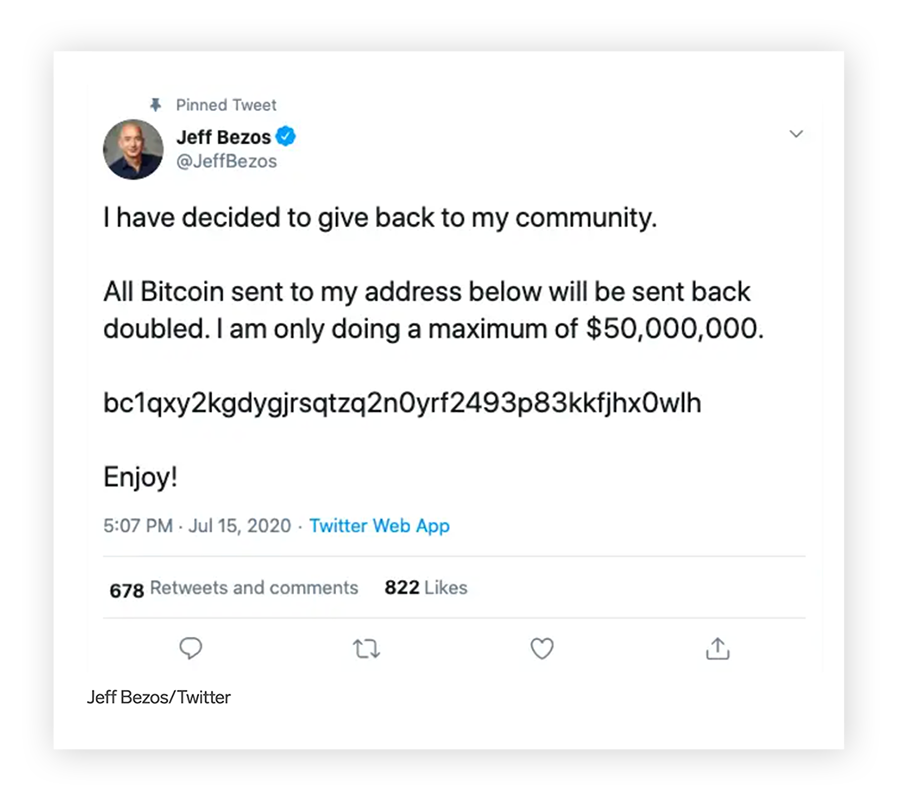 Whaling attacks target high-profile people.
Whaling attacks target high-profile people. 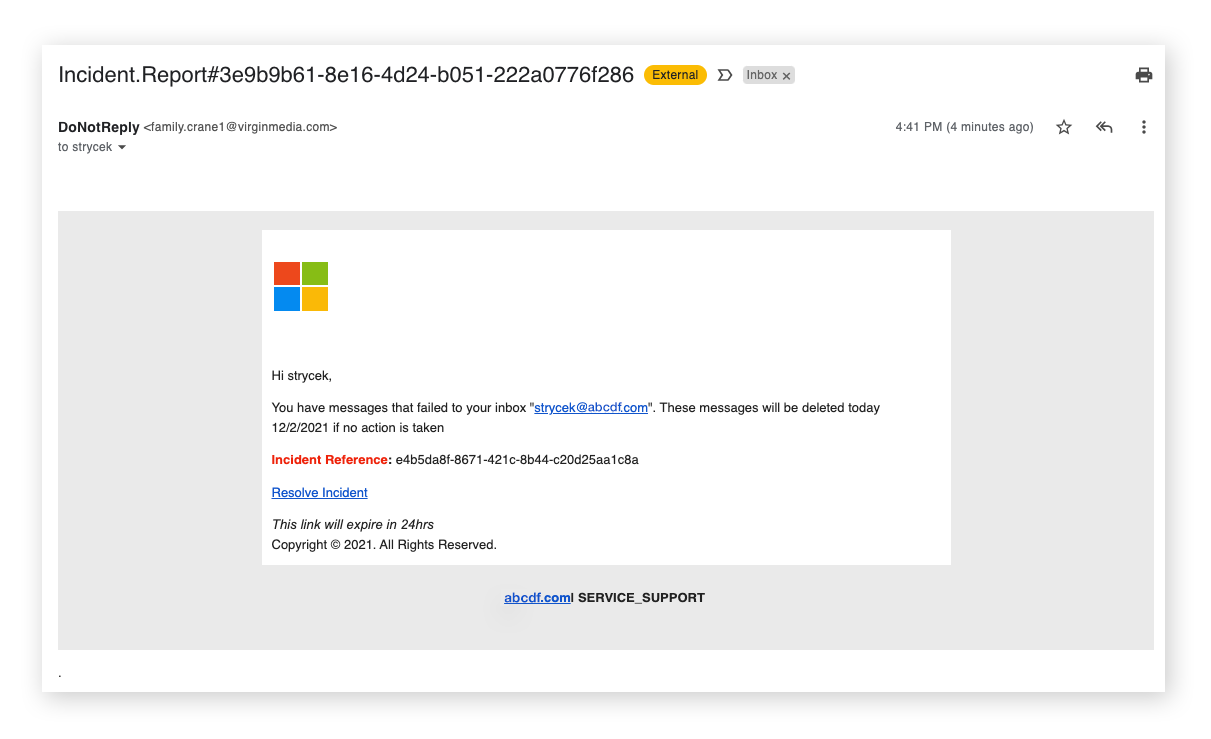 Check that communications you receive from brands are legit.
Check that communications you receive from brands are legit.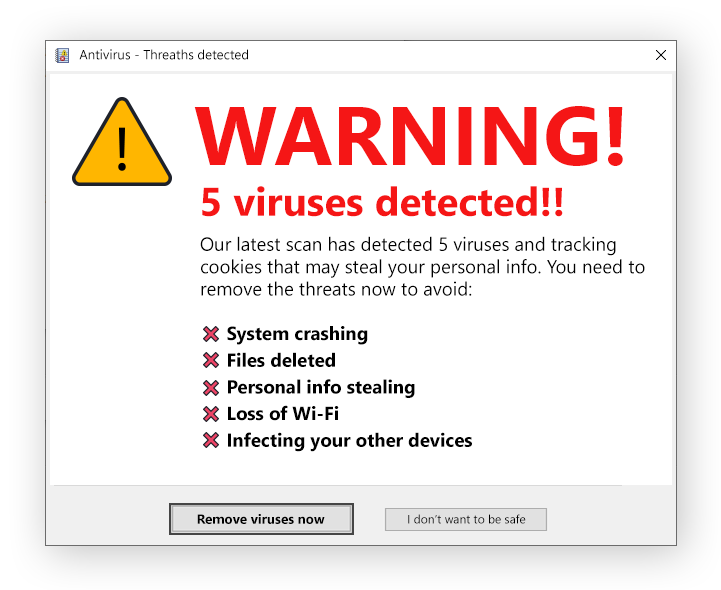 Scareware tries to convince you that you have malware on your device.
Scareware tries to convince you that you have malware on your device.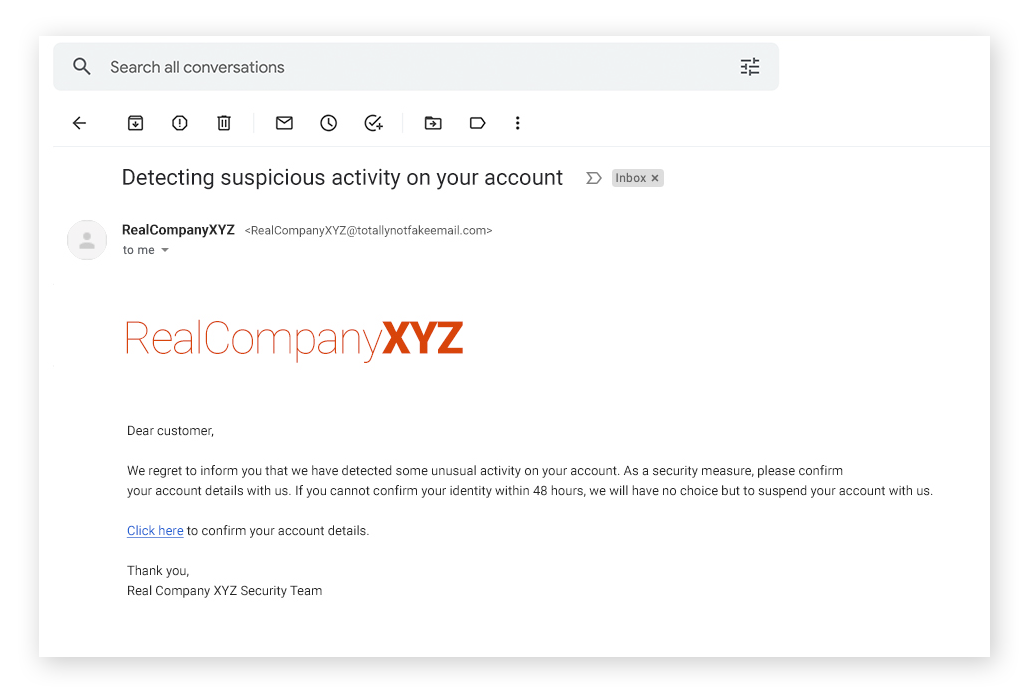 Signs of a spoofing email include fake email addresses, suspicious links, and missing or fake contact information.
Signs of a spoofing email include fake email addresses, suspicious links, and missing or fake contact information.




