It’s Jenny’s baby shower and all the girls are chatting it up, talking about how excited they are for this bundle of love and joy to enter the world thrashing and screaming. All of the sudden, Becky, who’s a total sweetheart, whips out a giant rum cake to surprise the special mom-to-be. But then, she wonders, is it safe for a pregnant woman to eat rum cake? They take out their phones to check, but when they go to Cake-babies.com, they find they cannot access the site. Every other website works fine, but for some reason, this one just won’t load.
There’s a halfway-decent chance that your baby-and-cake website is currently undergoing a dreaded Denial of Service attack.
What is a DoS attack?
A DoS, or a Denial of Service attack, is a concentrated effort by hackers to limit or completely eliminate web traffic to a particular website, server, or online service.
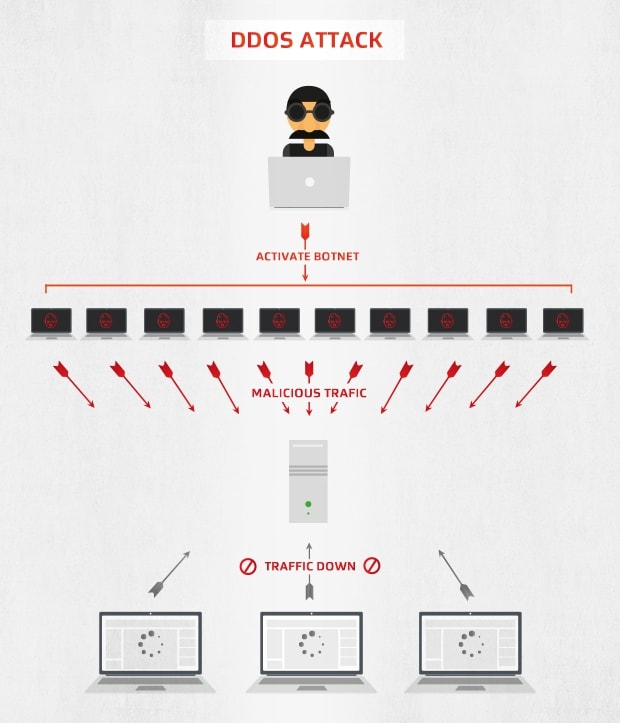
There are a lot of ways one can perform a DoS attack, the most famous and prevalent being a DDoS — or “distributed denial of service” — attack, which involves forcing or tricking a bunch of computers into flooding a server with data to the point where it can’t be used. We’ll talk about that in a bit more detail below.
A DDoS attack floods a server with so many requests that it becomes unresponsive — effectively shutting its service down
As for why people perform DoS attacks, that’s a bit tricker. The most common, but far from the only, reason is cyber-activism, a way to protest a website or organization that the attackers disagree with in some profound way and want to either shut up or intimidate. But they can also be pranks, a ransom threat, an attempt at extortion, or a distraction for a more serious, damaging hack going on in the background. And sometimes, they’re merely used to test how capable a server is.
DoS attacks have been carried out against everyone from financial institutions to electronic outlets to video games to religious groups, and even governments. They’re a staple of the online hacking world and they probably aren’t going away anytime soon. But there’s a better-than-good chance that it’s not really your problem.
Still, you came here to learn, and learn you shall.
How does a Distributed Denial of Service attack work?
A DDoS attack is a simple premise: crowd a server with pointless traffic so the websites it hosts runs slowly, if at all. But since nothing on the internet is simple, explaining how that works will require a bit more technical detail.
Let’s try to keep it as simple as possible, shall we?
Some internet basics
In 2006 US Senator Ted Stevens became a meme for describing the internet as a “series of tubes”, and while that’s flawed in many ways it might be the best analogy for the situation, so lets work with it. Basically: any time you try to do something online, be it send a message, go to a website, or play a game, your computer has to communicate with another computer and/or server. To do that, they need a carrier, such as the air for WiFi, or copper wire/fiber optics if you’re connected with LAN cables. The rate at which the carrier can transmit data is called bandwidth: so for the purpose of this analogy, bandwidth is the size of the tube, with a bigger tube allowing more information to flow faster.
The thing is, you always have to share your bandwidth/tube with other computers, all of whom are also trying to send messages, go to websites, or play games. This means tubes can fill up pretty quickly, and if you try to use a tube that’s already full, you could muddy all the data that’s already in there.
A bad but useful analogy: think of the internet as a series of tubes — and a DDoS attack as clogging those tubes up
There are a few ways we try to keep that from happening: the first is Collision Domain, which reduces networks into multiple yet connected tubes. Think of water: if you connect several tubes and fill one with water, then that water will spread equally across all the tubes. Data acts the same way, spreading across the entire tube network looking for a specific computer or server, and that takes up both space and time. So to keep that from happening, we use separate but connected ‘domains’ that act as a kind of checkpoint: if your data tries to get through and the checkpoint realizes that it's trying to reach a computer or server not in its domain, it rejects your data’s attempt to enter so the tubes it protects remain unpolluted with your data. The internet is basically that on a international level.
But the second — and more important one for our purposes — is something called Exponential Backoff. If your computer tries to use a tube and notices that it’s full, it will wait a second before trying to use it again, hoping that by then it’ll be clear and it can fill the tube with its own data. But if it’s still full, your computer will wait two seconds (and a random interval of milliseconds) before trying again. Then four. Then eight. Then sixteen. And the number will keep going up until it either goes through or stops trying altogether.
What’s this have to do with DDoS attacks?
A DDoS attack — Distributed Denial of Service — is an attempt to fill up a server’s tube/bandwidth with so much data that exponential backoff will either slow websites down to a crawl, or make them entirely impossible to access. To do that, you need a lot of data, which, in the case of DDoS attacks, is computers trying to access a server. Which means that to organize such an attack you either need a lot of very well coordinated friends around the globe, or more realistically, you’re gonna need a botnet.
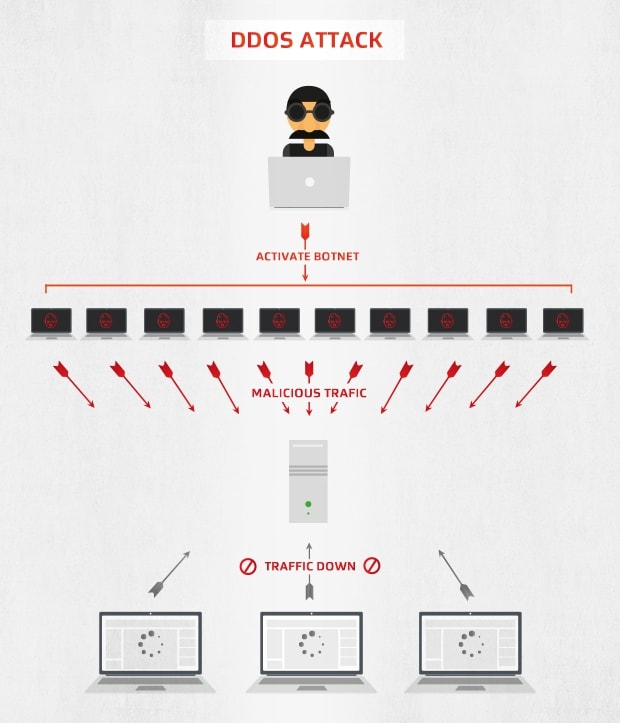
If you’re too lazy to click the link above, they’re basically they’re a giant collection of computers and internet-enabled devices connected via malware that a hacker can command to do all sorts of messed up stuff, from sending out waves of spam to hacking passwords. They can also, of course, orchestrate DDoS attacks.
One more layer of complexity
Don’t go thinking that the botnet will be attacking the target itself: only lazy and inefficient hackers would do that. The best DDoS attacks add an extra layer of complexity (and protection for themselves) by instead tricking innocent computers into doing their dirty work for them. These innocent computers, called “reflectors”, are sent a misleading connection request from one of the “zombie” computers in the botnet. That contact request will trick the reflector into thinking the target server is trying to reach out to them, and like a good machine it will try to reach back in order to see what it needs. You get enough innocent “reflectors” all pinging the server at the same time, and you’ve got yourself a DDoS attack.
Even innocent and uninfected computers might be roped into participating in a DDoS attack by becoming "reflectors"
This method is prefered for two reasons. First, it’s far easier to send out these connection requests than it is to manually try to DDoS a website yourself, and it allows smaller botnets to trick much larger networks into doing the hard work for them. Secondly, it provides an extra protective layer between the hacker and the server being attacked, making it harder to trace it back to them.
Hackers can also target specifically sections of a website or service using this technique, called an application layer DDoS attack, to shut down particular features (like, say, the search function). Typically this is done in order to distract IT professionals while a much more important or damaging hack is taking place.
The IoT problem
Back in the past, DDoS attacks were a bit trickier to pull off, because it required a lot of internet-enabled devices and there was only really one to go around: computers. But in recent years, more and more devices are able to connect online, which allows botnets to grow bigger and bigger. With more objects, there are more pings and opportunities to fill a “tube” with data, so in some respects we’re living in a golden age of DDoS opportunities. What fun!
You can check out our ultimate guide to botnets for more.
Other kinds of DoS attacks
Of course there’s more ways than the ol’ DDoS to block a website! There are a host of other popular tools and techniques to execute a Denial-of-Service attack, even if DDoS is by far the most common.
-
Teardrop attacks send mangled IP addresses and oversized data packets to the target computer to either slow them down or crash them when they try to make sense of it.
-
Banana attacks create a feedback loop by forcing all outgoing messages a target sends out back into the target, which causes more messages, and makes everything crazy.
-
Smurf attacks take advantage of misconfigured network devices to send massive files to every connected device at once, blowing up the network.
-
PDoS (or Permanent Denial of Service) attacks involve hacking into IoT devices and completely replacing firmware with something corrupt or defective.
-
Nukes involve sending corrupt error messages or operational information data to the target, slowing it down until it’s completely frozen.
-
Peer-to-peer attacks have hackers breaking into a target’s network and instructing all the connected devices to try to connect to a single website or server at the same time.
-
Ping floods simply require you send a huge number of pings from one computer to another — a simple attack and a common tool when cheating in online games.
-
Degradation-of-service attacks have botnets attack a website in “waves”, so the website doesn’t shut down entirely, just slows down frequently and unpredictably.
-
HTTP POST attacks are an obsolete attack method that involved sending a target data, but broadcasting it so slowly that other data has to ‘wait’ for it to finish before going.
-
Denial-of-Service Level 2 attacks trick a target’s defense mechanism from blocking the network from the internet, taking everything offline.
-
The Ping of Death is a malicious, malformed ping larger than 65,535 bytes, which causes some systems to crash when they try to handle it.
-
Amplification attacks manipulates publicly accessible DNS to send DNS traffic to unprepared sites, like a bigger version of a reflector attack.
-
Slowloris (or RUDY) tries to hog as many connections to a website or service as possible for as long as they can, to limit availability to legitimate users.
-
Shrew attacks target the Transmission Commission Protocol with quick bursts of activity to exploit timeout mechanisms and slow down legitimate traffic.
And that list just keeps growing as people discover new vulnerabilities and craft new tools to plug holes and disrupt traffic.
Who is targeted by DoS attacks?
If you’re sitting in your underground bunker terrified that “the man” is going to try to DDoS you to keep you from discovering the truth, you can go ahead and lift the aluminum foil off your head. DoS attacks are never performed against individuals: they’re all performed against servers to take down specific websites (and any other websites that might incidentally be hosted on said server). Plus, unlike most other online attacks, there’s no financial or practical benefit to randomly attacking sites with a DoS: they’re always done with a purpose, so unless you host controversial data (or you’re a controversial figure with a blog or a website or something), you don’t really have to worry about getting bombarded by one.
Are DoS attack legal?
In theory, no. In practice… well…
Basically, performing a DoS attack on any organization or website is considered a crime, although not a terribly bad one. In most cases, it’ll get you about a year behind bars and a hefty fine, although if you DoS something serious (like, say, a police station), then other charges could be tossed on top of those. There have been people who’ve argued that it should be a legit form of protest, but by and large, getting caught DoSing will bring you trouble in the US and UK.
But in practice, the legality of DoS attacks are up in the air. Namely, governments can and have used DoS attacks in the past (see below) as a form of cyber-warfare, and organizations can target themselves with DoS attacks to test server capacity and/or their cybersecurity team. So while you shouldn’t be doing DoS attacks anyway, just know that getting caught will also get you in a spot of trouble.
Famous examples of DoS Cases
There have been a lot of DoS attacks in the history’s relatively short history. Let’s look at a few examples, shall we?
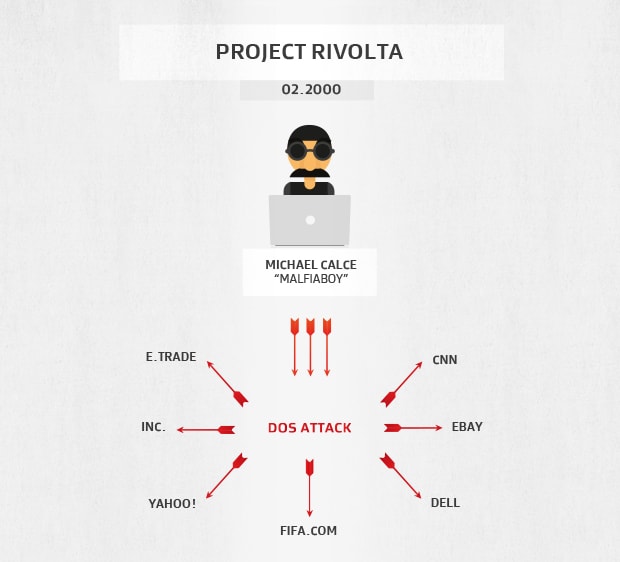
Project Rivolta — turn-of-the-century terror
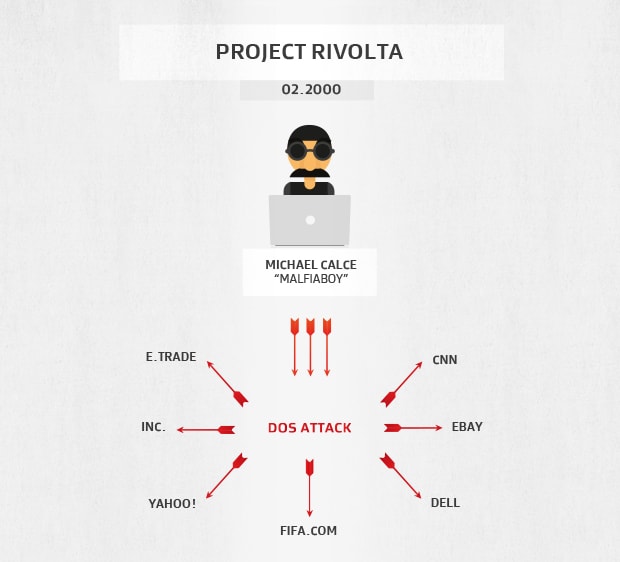
As the clock struck midnight and the year 2000 rang in, people held their breath in horror, fearful of the Y2K bug. Nothing ultimately came of that largely ill-founded anxiety, but there was another internet cataclysm lurking in the wings: Project Rivolta. On February 7th of that same year, a Canadian master hacker named Mafiaboy launched a massive DoS attack that took down the biggest websites on the net at the time: Yahoo!, Fifa.com, Amazon.com, Dell, Inc., E*TRADE, eBay, CNN, and more. He did it by breaking into each network and installing “sinkhole” software, which flooded the targets with aggressive traffic — a PDoS attack.
This was a huge deal: not only was this one of the first DoS attacks ever performed, it lasted far longer than your standard DoS attack, restricting access to what was effectively the whole internet for a full week before the sinkholes could be removed.
Project Rivolta was the first DoS attack
An international manhunt was organized to capture the perpetrator, and thanks to his big mouth (he bragged about it a lot online), Mafiaboy was caught: and discovered to be a Canadian high schooler named Michael Calce. They sentenced him to 8 months in a detention center, with limited internet access.
The DoS only lasted a week, but the knowledge that the internet could be “broken” by a 15-year-old? That had a much larger impact, damaging the worldwide economy and leading many people to seriously reconsider online security.
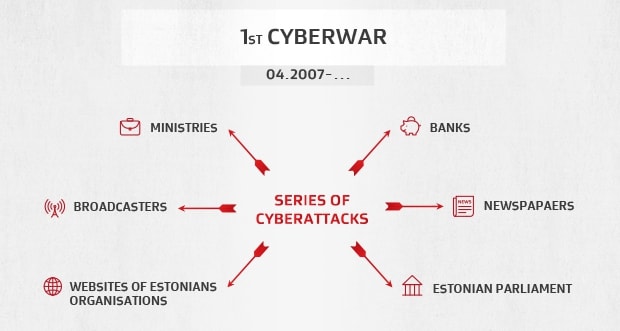
The 2007 Estonia attacks — the first cyberwar
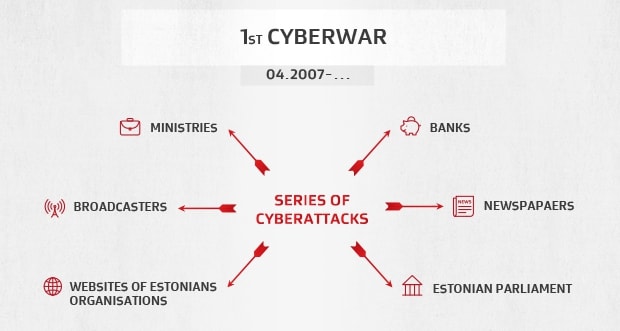
These days, cyberwarfare is a common and expected thing, with governments frequently hacking, spying, and infecting each other in order to gain an upper hand over friends and foes alike. But in 2007, that shadowy world was exposed to the public when dozens of websites run by Estonian, organizations and businesses were shut down due to a country-wide DoS campaign, ranging from ping floods to DDoS attacks.
Banks, newspapers, and even parliament were all targeted, and were down for upwards of several weeks, which soon sparked riots all throughout the already unstable country. People couldn’t access their money, government employees could barely communicate, and keeping up with the news became basically impossible. By the time the situation could be contained and fixed, the damage had already been done: 150 people had been injured and one killed in all the rioting.
The assault on Estonia cemented DDoS's place in the arsenal of cyberwarfare weapons
As with most cyber attacks, tracking the sources responsible proved difficult. International investigators pinned the blame on Russia, due to the fact that the attacks came from Russian IP addresses, online instructions were in the Russian language, and Moscow offered no aid when Estonia asked for it, but so far the only man charged was one Estonian nationalist who could be directly tied to the attacks. He was fined.
As a direct result of this attack, the NATO Cooperative Cyber Defence Centre of Excellence was founded in Tallinn, Estonia.
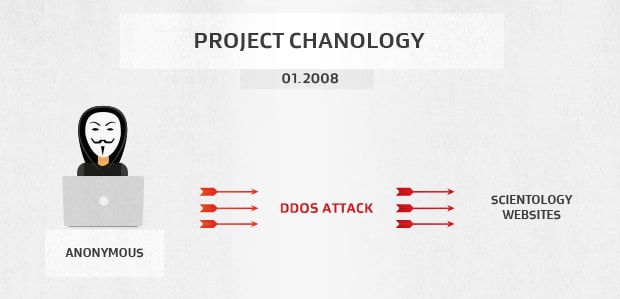
Project Chanology — rebels with a cause
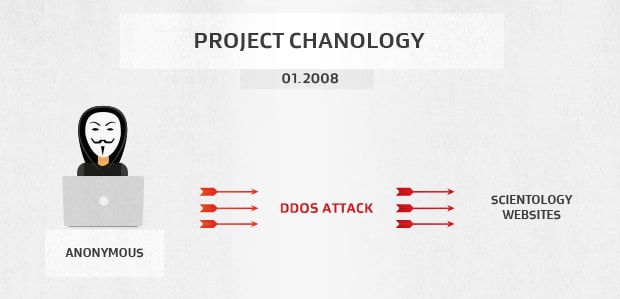
Before 2008, “Anonymous” was just a group of jokers online who occasionally messed around but were largely inconsequential. After 2008, they became the face of the deep web and would be talked about as if they were some kind of formless online deity. And Project Chanology is largely to blame.
An online campaign against the Scientology group, Project Chanology marks the first time DoS attacks were used as a form of protest, with the group objecting to just about everything the organization stands for. While performing DoS attacks against Scientology websites was the primary attack method, they also leaked documents, performed long-distance pranks to annoy and inconvenience the church, and held live protests in their iconic Guy Fawkes masks. And this continued for well over a year.
While blows were traded on both sides, both Scientology and Anonymous remain, albeit vastly changed from the experience. But the biggest legacy left by Project Chanology is that it would go on to inspire countless other forms of online protest both inside and outside the group: for example, in 2010 Operation Payback, Anonymous performed DDoS attacks against the Motion Picture Association of America, the International Federation of the Phonographic Industry, and other copyright holders in protest to attacks made against piracy websites. Another random example: in 2016, several hackers DDoS’d the Thai government in protest of strict internet regulation.
One thing is for sure: this spat with Scientology has cemented the DDoS attack place in protesting history.
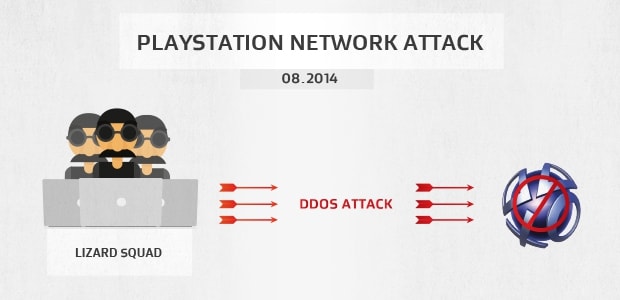
The 2014 PlayStation Network attack — setting an example
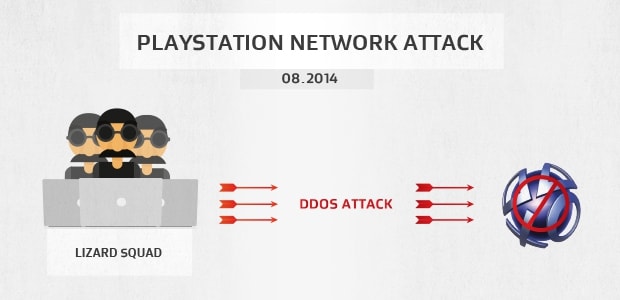
In August of 2014, the PlayStation Network (which is how PlayStations connected and gamed online) was rendered unusable by a large-scale DDoS attack, which knocked down the servers and rendered tens of millions of people unable to play games online.
The hackers behind the attack, the now-defunct Lizard Squad, claimed that the attack was orchestrated by terrorist group ISIS, and that they had also planted a bomb on the plane that Sony Online Entertainment president John Smedley had been flying on during the attack. The plane landed without issue.
DoS attacks are fairly common in the gaming world, so in the great scheme of things there would be nothing particularly special about this attack… were it not for the fact that the PSN had suffered an enormous hack and data breach in 2011 that left Sony reeling and promising to improve their online security. This hack, a mere three years later, was significantly smaller, but did a good job damaging consumer trust in Sony even further, and showing how powerless or apathetic companies can really be in the face of the modern online world.
Kind of a bummer, that one.
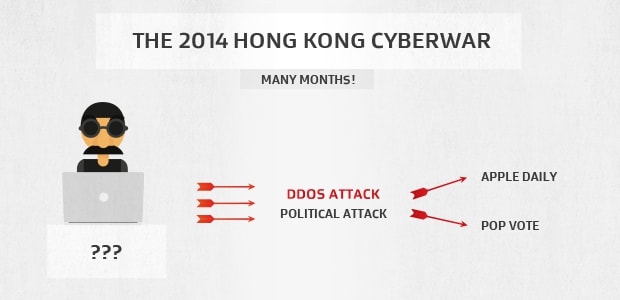
The 2014 Hong Kong cyberwar — an attack like no other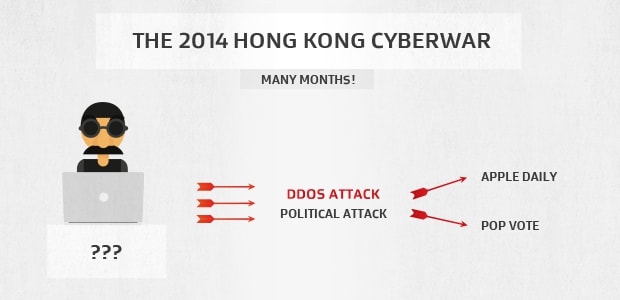
Estonia might have been the first country to be DoS’d in a political attack, but they weren’t the last, or even the biggest. That honor belongs to the independent press in Hong Kong, which was DDoS’d for not days or weeks, but months as the “Occupy Central” protests grew larger and more violent.
Websites Apple Daily and PopVote, who orchestrated mock elections and promoted the pro-democracy marches that had swamped the city of Hong Kong, found themselves on the receiving end of an unprecedented DDoS attack, with over 500 gigabytes of “junk traffic” being streamed into their servers at a time with the help of hacked Amazon and LeaseWeb servers, rendering them almost entirely useless. Eventually, the parent company of these two websites, Cloudflare, was caught up in the DoS as well.
It added up to 250 million DNS requests per second.
Unfortunately, the DoS attacks only ended when the protests were forcefully broken up in December of 2014, with 955 arrests, 255 injured protesters, 130 hurt police officers, and China no closer to free elections.
What can you do to protect against DoS Attacks?
Not much, is the long and short of it.
Outside ensuring your computer isn’t part of a botnet (so install an antivirus, improve router security, and update your connected device’s passwords) to ensure you’re not directly contributing, it’s outside your power to prevent these from happening. And even if you’re not part of one, there’s not a lot you can do if your computer is one of the ‘reflected’ devices, as that trick exploits legitimate computing practices.
That said, if you happen to run a server or you’re a web administrator, you have a few tools at your disposal to deal with many kinds of DoS attacks, if you’re quick enough to catch them:
-
Dead traffic can be redirected to a “black hole”, a non-existent server where they won’t bother anyone.
-
There are bandwidth management tools that can examine and identify potentially risky data packets and block them before they access your network.
-
Upstream filters can use “scrubbing centers” to filter out bad connections and only allow good ones to reach the network.
-
And there’s always the option of renting more bandwidth to accommodate all the extra “traffic”.
Firewalls, which we happen to offer in AVG AntiVirus Business Edition, can also block extremely simple DoS attacks if you instruct it to block all traffic from a certain problematic IP address.
But for the average user? It’s not really something you can control. You’ll have to ride it out, or maybe use another service for the time being. There are worse fates than using Hulu, right?
Tools of oppression. Tools of protest
The DoS attack is here to stay, for better or for worse.
While it’s typically easy for us to condone all forms of online attacks, DoS attacks take a very particular space in the online threat landscape. They are tools for oppression, but they are also tools for protest. They’re inarguably bad, but also far better than leaks and doxxing. They hurt common people, but the average person is never the target. While we want to live in a world where DoS attacks don’t exist, it would be far better to exist in a world where they didn’t need to.
And there might be nothing the average user can do to stop it from a technical aspect, maybe we could help make that ideal world a little bit closer to becoming a reality. But, that’s getting ahead of ourselves, isn’t it?
All the same: stay safe out there!
%20Attacks/What_is_a_DDoS_Attack-Hero.jpg?width=1200&name=What_is_a_DDoS_Attack-Hero.jpg)