What is vishing: a definition
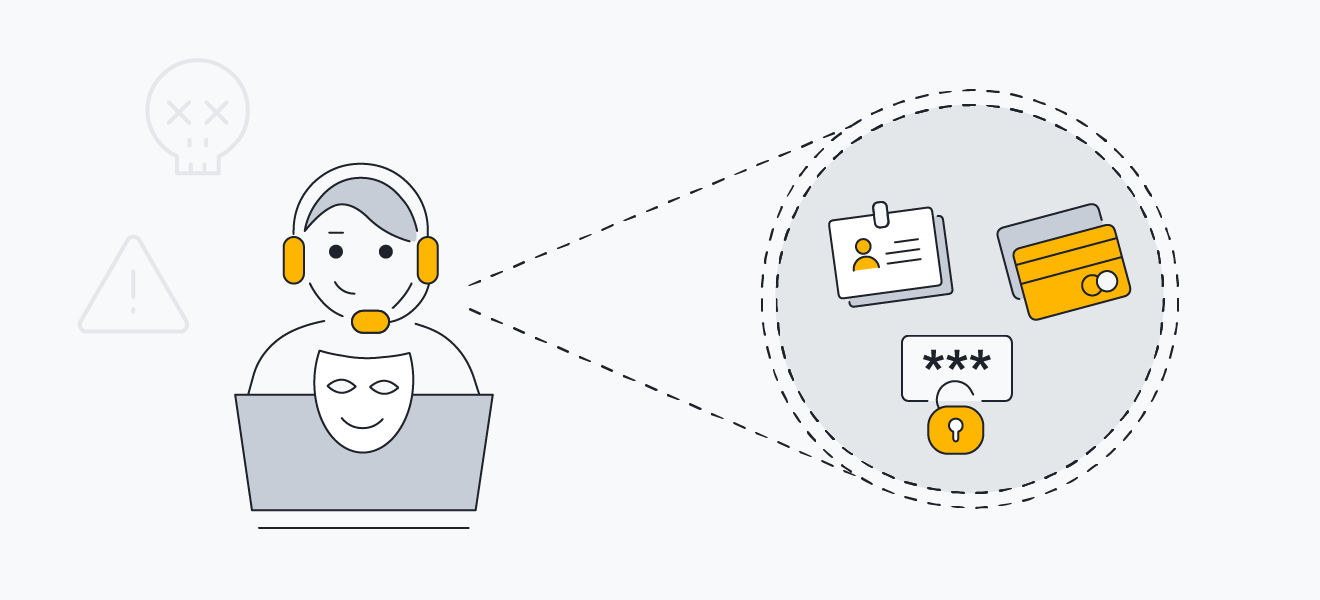
Vishing, or voice phishing, happens when a supposedly reputable person or company uses phone calls or voice messaging services to convince victims to reveal personal information. In a vishing attack, scammers (or vishers) pose as trusted sources in order to get sensitive information, like credit card numbers or government IDs.
Vishing scammers usually spoof a local number or a trusted business number to get through to their victims. Sometimes, they use vishing to implant malware on your device, which allows them to harvest your information in a different way.
Anyone with a phone number can be a target of vishing — individuals and businesses alike have fallen for vishing scams. And because of the use of sophisticated social engineering tactics, anyone can fall for a vishing scam.
Vishing vs phishing
Phishing refers to any scam where scammers pose as legitimate sources and manipulate victims into handing over personal information. Vishing is just one of several types of phishing scams, and is specific to voice phishing — phishing attacks through the use of phones or voice messages.
There are plenty of other phishing types out there, too. Spear phishing is when a scammer targets a specific individual or organization, social media phishing looks like a lighthearted post on your Facebook wall asking you to give answers to common security questions, and smishing is phishing via SMS messages.
Regardless of the method, all phishing attacks have the same goal: to obtain personal information in order to steal money, commit identity theft, or otherwise take advantage of their victims’ sensitive details.
Common examples of vishing attacks
There are many examples of vishing attacks and various techniques used to carry them out — new vishing scams pop up all the time. Some common vishing techniques include wardialling, VoIP vishing, caller ID spoofing, and dumpster diving. Medicare and tax scams are common vishing scam topics.
Here are a few examples of vishing attacks:
 Wardialing
Wardialing
Wardialing (or war dialing) is the use of software that automatically scans lists of telephone numbers and dials dozens of numbers quickly. This software is often used to find phone numbers connected to telephony devices — devices that aren’t phones, but have the capability to make phone calls over the internet.
While this alone can be a harmless annoyance for anyone who picks up the phone (the software is usually programmed to hang up), hackers use wardialing for more nefarious purposes, too: to find human victims with a Voice over Internet Protocol (VoIP) account to target for their scam. War dialing is also used for robocall scams, which rely on pre-recorded messages instead of human scammers.
 VoIP
VoIP
Rather than landlines, vishing primarily targets numbers connected through VoIP. VoIP services work like landline or cellular phone numbers — only they work exclusively over the internet. VoIP phone numbers are less dependent on a specific physical location to work. As long as there’s an internet connection, the same number can make phone calls worldwide.
While VoIP has obvious advantages, the anonymity and lack of geographic specificity to VoIP numbers make it easy for would-be scammers to exploit. Vishers can download and set up their software, prepare a script, and go on a calling spree with hardly any costs other than their internet connection. And, their real identity is likely to remain a mystery.
 Caller ID spoofing
Caller ID spoofing
Another tool that vishers use is caller ID spoofing. Often part of VoIP services, caller ID spoofing (not to be confused with IP spoofing) involves tricking the victim into thinking the caller is someone else. In the case of vishing, scammers spoof an official or local source to encourage the victim to pick up. Thanks to modern technology, caller ID spoofing is easy for scammers to get away with.
 Dumpster Diving
Dumpster Diving
Dumpster diving is the practice of going through someone else’s trash in hopes of finding treasure. For scammers, the treasure is lists of personal information on documents that organizations or households carelessly throw away. The information they find may include phone numbers, names, addresses, credit card details, and more — allowing scammers to better trick victims into trusting them.
 Credit card fraud
Credit card fraud
Credit card scams are among the most common examples of vishing. Scammers claim to be a representative of your credit card company, saying that your credit card has been compromised. They ask for your credentials to help them “solve” the problem. Once they have the information they want, the call is wrapped up quickly and the victim finds their credit card maxed out.
 Medicare or social security scams
Medicare or social security scams
Medicare and social security scams involve the impersonation of an official representative from one of these government-run agencies. They will often claim there is a problem with your account, or offer a new benefits card — either way, they ask for personal information that shouldn’t be freely given out. These types of vishing scams typically target older people, who may be more trusting of phone calls and less knowledgeable about technology and scams.
 Tax or IRS scams
Tax or IRS scams
Tax scams and IRS scams — where scammers pose as tax officials — have become particularly common in recent years. Tax scammers may say there is something wrong with your tax return or that you owe additional taxes. Then, they ask you to verify your identity by disclosing otherwise private information. If victims initially refuse, scammers threaten to cancel their benefits or arrest them in order to scare victims into compliance.
How criminals execute vishing scams
Criminals execute vishing scams by using a combination of technical tricks — like caller ID spoofing and internet phone calls — and social engineering. Using known information about their victims, scammers can more successfully manipulate people into falling for their vishing scams.
Social engineering takes advantage of humans’ tendency to trust certain institutions or forms of behavior in order to trick people into doing something. Vishing scammers impersonate a trusted source — such as government officials and bank representatives. Tech support scammers pose as technical experts to gain victims’ trust and get them to install malware or hand over access to their device. Regardless of the ultimate aim, social engineering is often the means scammers use to get the information they want.
Creating a sense of urgency is another tactic fraudsters use. While impersonating a trusted source, vishing scammers often stress the seriousness and immediacy of the supposed problem to get victims to act quickly. This ensures victims are less likely to question the caller or check the veracity of the scammer’s claim, making them more likely to fall for the scam.
How to prevent vishing scams
To prevent vishing scams, don’t answer calls from unknown numbers, and don’t give out private information over the phone. If you suspect the caller is a scammer, simply hang up. Remembering these tips, plus learning how to spot vishing and other phishing scams will help prevent you from becoming a victim.
The success of vishing scams hinges on human error, and vishing prevention is best done by making yourself aware of human vulnerabilities. Study the common vishing examples above to know when to be on guard.
You should never give out or confirm private information over the phone. Generally, most companies don’t call you to request such information. Don’t call any phone numbers they provide to validate them, either — use Google or another reliable source instead to find the information you need.
If you think you’re on a suspicious call, you should ask the caller for more specific details, reasons for the call, or how they got your number. And while it may be rude, you can also just hang up if you suspect a scam.
 Vishing scammers may already have personal information about you, but never confirm it over the phone.
Vishing scammers may already have personal information about you, but never confirm it over the phone.
Registering your number on the Do Not Call registry (in the US) or Telephone Preference Services (UK) might prevent some unsolicited sales calls, but it’s far from perfect. After all, scammers are not likely to respect your request not to receive unsolicited calls.
If you don’t often have unidentified numbers calling your phone, you can simply avoid answering any unknown number that tries to contact you. If a visher leaves a message claiming to be a part of a known organization, contact that organization directly rather than returning the call.
Many of these prevention strategies can work against scams of all kinds — both online and off. But to keep you and your private information better protected, strengthening your online security with antivirus software and other tools can make a big difference.
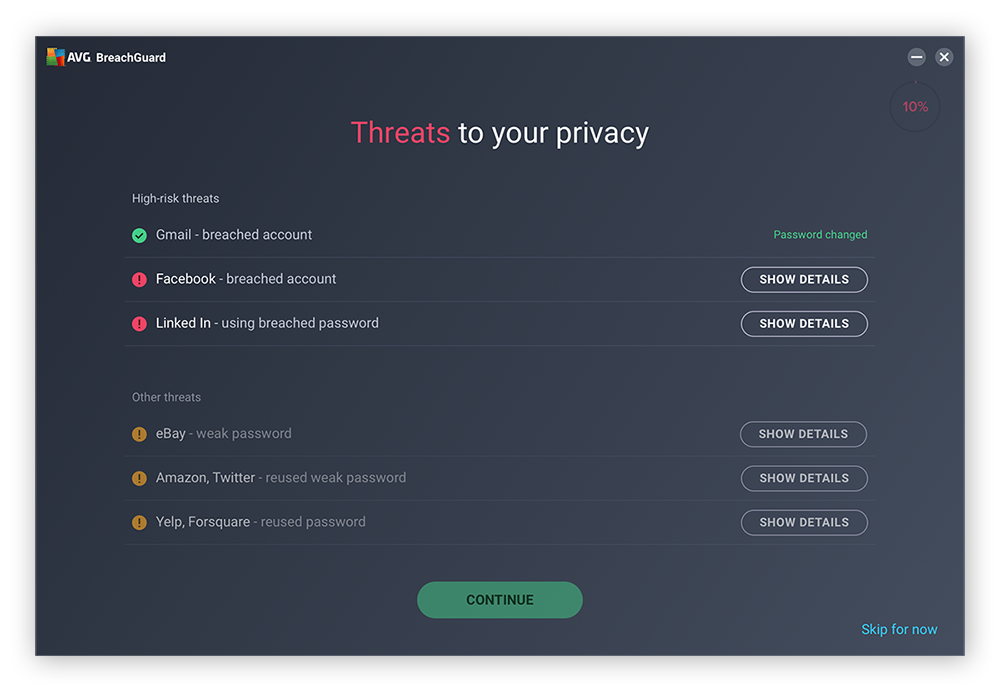
Protect yourself against vishing scams with AVG BreachGuard
Scammers will stop at nothing — even the trash — to get their hands on personal data. Unfortunately, keeping your private data secure can be difficult with so many online accounts and services that have access to it.
AVG BreachGuard makes it easy to keep your data private, by constantly scanning the dark web for evidence of data breaches that include your information. BreachGuard’s built-in Risk Monitor works 24/7, allowing BreachGuard to alert you of a data breach as soon as it happens.
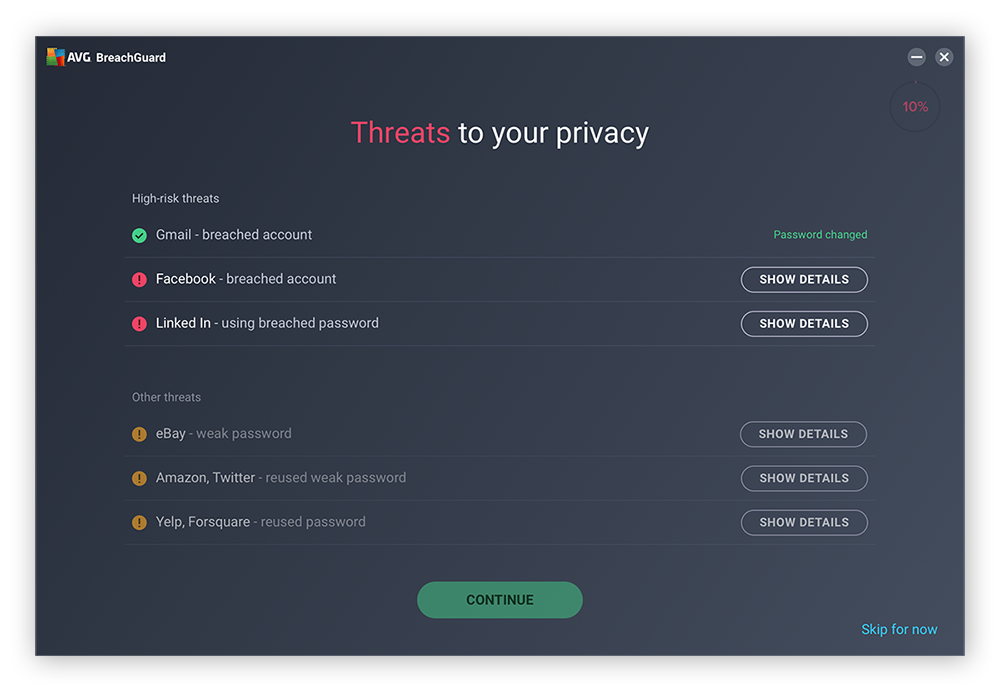
AVG BreachGuard also helps you retain control of your personal data, by automatically requesting that data brokers remove your information from their databases, helping to prevent third parties (including scammers) from obtaining your address, phone number, and other private data.
AVG BreachGuard helps secure your information and assists you in making sure you’re aware of the personal information you share with major organizations. Get AVG BreachGuard today and start protecting yourself against vishers and other scammers before it’s too late.

 Vishing scammers may already have personal information about you, but never confirm it over the phone.
Vishing scammers may already have personal information about you, but never confirm it over the phone.