How does 2FA work?
Two-factor authentication works by requiring two forms of identification to verify your identity and grant access to your account. 2FA uses two of the following three factors to verify your identity: something you know (like a password), something you have (like a key), or something you are (like a fingerprint). By adding an additional verification step, 2FA significantly strengthens the security of your accounts.
When you sign into any of your online accounts, the basic level of authentication requires only your password to log in — that’s step one to verify your identity. 2FA requires a second step before you can get access to your account. The second step relies on something you know, something you have, or something you are. In addition to entering your password, for example, 2FA might also require you to enter a one-time PIN code sent via SMS to verify your identity.
How 2FA works in detail
2FA works by verifying a second piece of information in addition to your password. Because 2FA requires two unrelated pieces of data, there’s very little chance someone can access both. The type of authentication info depends on the online service you’re using, whether it’s Facebook, iCloud, Yahoo, or Google.
For example, Gmail gives you a few choices when setting up 2FA:
-
A physical security key: This option functions like a lock and key, which you usually need to purchase.
-
The Google Authenticator app: First, you need to install the app on your phone. Then, each time you sign in to your email, you receive a prompt on your phone that you need to tap to verify it’s really you.
-
Verification code: This option sends you a one-time numeric code, usually by SMS, that you need to enter to verify your identity.
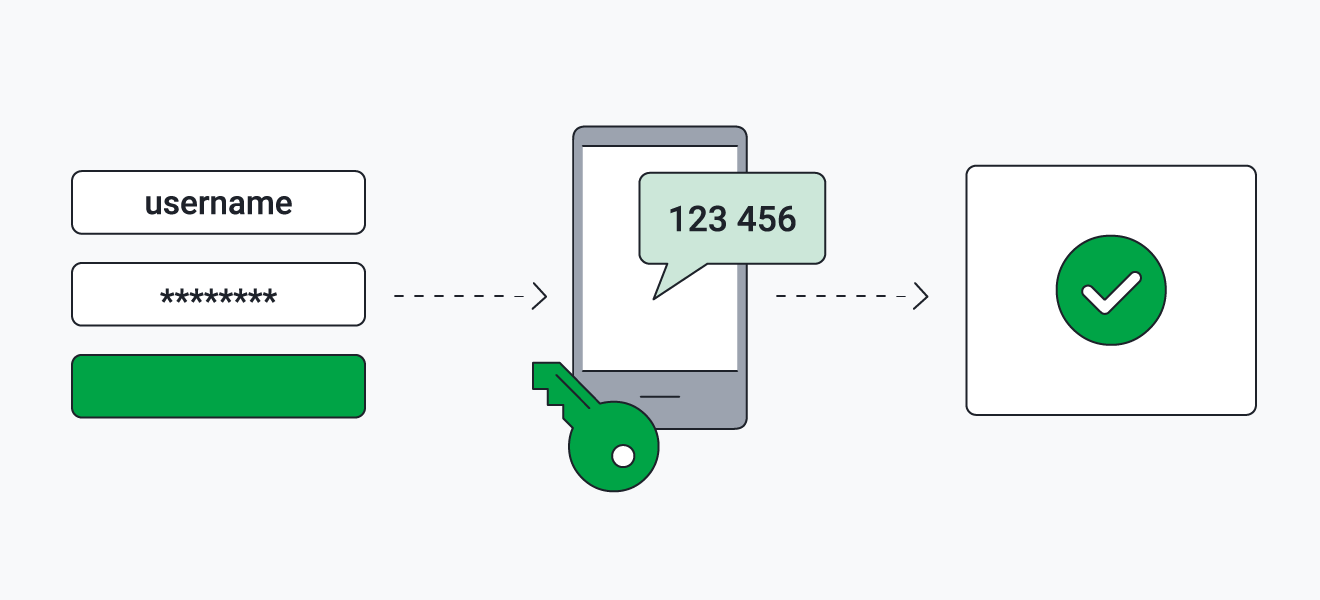
Here’s how 2FA works when you want to access your account: You type in your username and password and click submit. Then, the online service you’re logging into then sends an automated request for your second piece of info, which may be an SMS with a verification code, a Google authenticator prompt, or some other 2FA method you set up. After verifying the second piece of info (the second factor of authentication), you get access to your online account.
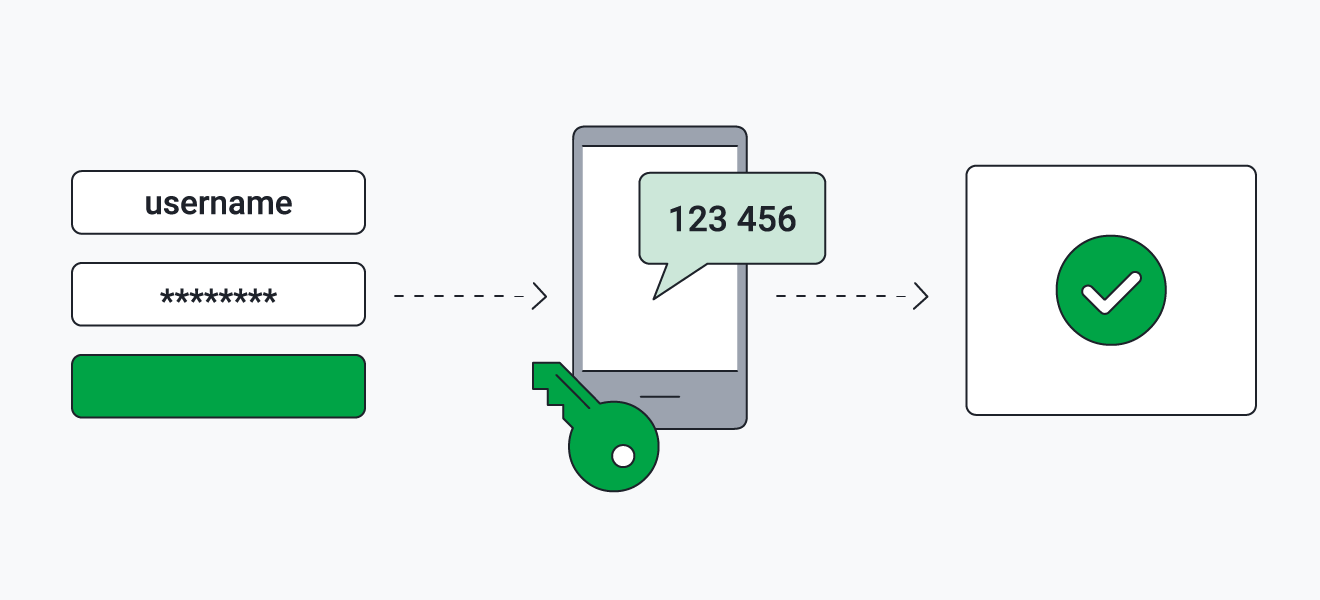 Two-factor authentication requires two forms of identification to verify your account.
Two-factor authentication requires two forms of identification to verify your account.
Without that second piece of information, a hacker trying to break into your account — even a hacker who has your password — is locked out.
The best description of two-factor authentication is that it’s a security measure requiring two different types of authentication in order to access an account. So, if you get a message with a passcode for verification and you haven’t recently tried to log in, you’re safe if you don’t do anything. But, you should change your password immediately to something unique, and use a secure password manager to keep track of all of your passwords.
For a more detailed definition of 2FA and to learn how you can use it to protect your digital identity, check out Michael McKinnon’s explanation of two-factor authentication, password protection, and why it's important for your online security.
The three basic authentication factors
2FA’s additional layer of authentication is generally one of three basic factors: something you know, something you have, or something you are. Here’s the type of information that fits into these three authentication categories:
-
Something you know: This could be a PIN code, the answers to security questions, and, of course, your password.
-
Something you have: This generally refers to a physical object, such as a credit card, a security token (a small hardware device), or an ID card. It can also refer to your phone, which you can verify possession of via SMS code or a special app like Google Authenticator.
-
Something you are: This refers to biometric data, and usually comes in the form of your fingerprint or facial scan — such as with Apple’s Touch ID or Face ID.
2FA happens every time you use an ATM. Withdrawing money from an ATM requires something you have (your bank card) and something you know (your PIN). But when you sign into an online account with your username and password, even though you’re providing two pieces of information, those two items don’t satisfy the criteria for 2FA, because both are something you know. Thankfully, most email accounts let you add an additional layer, like proof that you have your phone with you.
Your fingerprint is one of your most identifying features. Everybody's fingerprint is unique, and it never changes. But what if we told you those are big reasons never to use fingerprint locks? It’s counter-intuitive, but the use of these locks can actually compromise your security.
But 2FA doesn’t usually involve fingerprints, as we’ll see.
Types of two-factor authentication (2FA)
Accounts with 2FA enabled are much less at risk than those without, and it’s easy to set up and use 2FA. Here are some types of two-factor authentication you can find around the internet:
Hardware tokens for two-factor authentication (2FA)
A hardware token is a small device synced to your website or network. It cycles through randomly-generated strings of numbers. When you want to log in, the site or network will ask for the number that’s on the token right now, and only that number will log you in.
It’s not ideal because these little tokens can be hacked, and most people aren’t as attached to them as to their iPhone or Android phone, making them more easily lost.
SMS (text message) and voice-based 2FA
Smartphone 2FA is one of the most common types of 2FA, because almost everyone has their phone on them at all times. The website sends a code to the phone via SMS or voice call, and you log in by entering the code. If you protect your account with a strong password and lock your phone with a completely different password, chances are low that a hacker will crack both.
But, 2FA via SMS is quickly becoming less and less secure. A technique known as SIM swapping has allowed hackers to take over your phone number. It’s still quite uncommon, but companies have responded by shifting their emphasis elsewhere. It’s also why secure messaging apps are on the rise.
Software tokens for 2FA
The advantage of SMS-based 2FA used to be that a hacker wasn’t likely to get your phone and your password. Since text messages can now be intercepted, this advantage is gone.
That’s where software tokens for 2FA come in. They’re linked to the device, not the phone number, so installing the software on your phone or laptop will ensure that only the person with access to that device can log in.
Push notification for 2FA
Push notifications are even more secure than either SMS or software tokens. A push notification is sent directly to your phone, averting the possibility of SMS intercepting or someone remotely accessing your device. They’re great for avoiding man-in-the-middle attacks which is just one way that email accounts get hacked.
Other forms of two-factor authentication
Biometric 2FA is on the rise, meaning you may start using your fingerprint, facial recognition, or an eye scan to get into your devices. But it’s not perfect. That’s why developers are hard at work on technologies that recognize voice profiles, typing speed, and even the noise of your surrounding environment.
Examples of two-factor authentication
Apple uses two-factor authentication extensively with their customer’s devices. They take advantage of the robust security of the iCloud and its connections to all your devices. When they see you trying to log in and they don’t know if it’s you, they send a 2FA code to one of your other Apple devices, like your iPad.
Many companies have specially-designed 2FA solutions to keep their employees’ activities as hidden as possible, too. A hardware token is a secure verification option for those who play a critical role at a company.
Why should I use two-factor authentication?
You should use 2FA because it provides ironclad protection where even the strongest passwords fail. Even if you create a strong password, there’s still a chance it can leak. But even if someone knows your password, they can’t access your account if you have 2FA set up.
A password used to go far, but hackers have all sorts of innovative ways to compromise them. Here are ways that crafty hackers can figure out your password:
-
Data breaches: When a large organization is breached, millions of people’s usernames and passwords (and other sensitive data) can wind up for sale on the dark web. Cybercriminals can buy lists of these usernames and passwords and attempt credential recycling, where they try to use these credentials all around the web to see what accounts they can access. That’s one reason to never reuse passwords on multiple accounts.
-
Spyware: This insidious type of malicious software can spy on you and record all your activity. Keylogging software can discreetly record everything you type — including your usernames and passwords — and send it back to the hackers who installed the malware on your device.
-
Phishing: Phishing is a type of social engineering scam in which cybercriminals impersonate a business or trusted contact to trick you into revealing personal information. In this case, it could be a fake email asking you to confirm your username and password for an online service you use — but typing it sends your info straight to the scammer.
-
Social media: Though not exactly sophisticated, without 2FA, you run the risk of your Instagram getting hacked. Did you wish your mom a happy birthday this year? Adopt a new puppy? Buy a house? A hacker can see public posts and gain information to use against you, whether that info is related to your passwords or not. Be sure to check your Facebook for leaks, and watch out for signs that your phone has been hacked.
That’s why 2FA is so important. If your password falls into a hacker’s hands, but you use 2FA, your account is still safe. The extra verification step makes 2FA a powerful security measure.
How to set up two-factor authentication
To set up two-factor authentication, you first need to make sure that the online service you’d like to use it for — like your email, bank, and social media apps — offers it. Check out this link for detailed instructions on setting up 2FA on your Gmail account.
As an example, let’s go through setting up 2FA on your Facebook account.
-
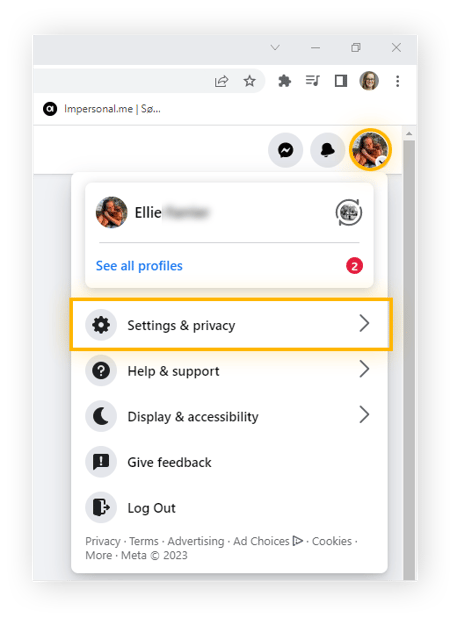
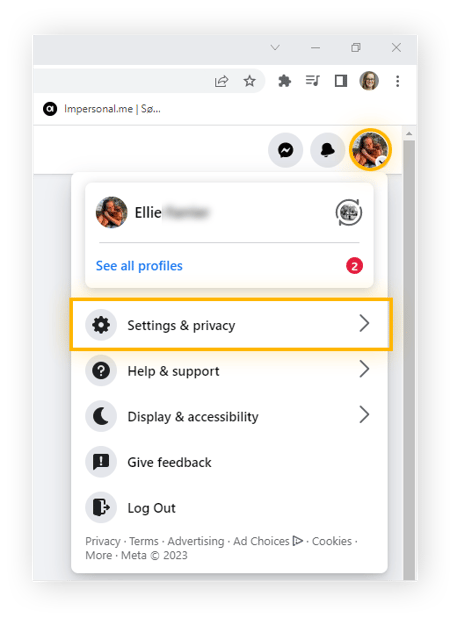
Go to Facebook and sign in to your account. Click your profile picture in the top-right corner and select Settings & privacy > Settings.
-
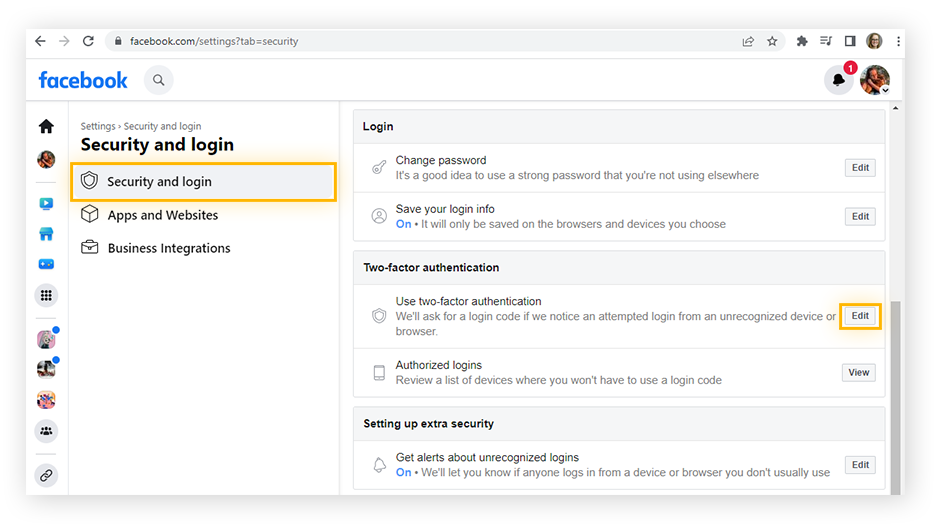
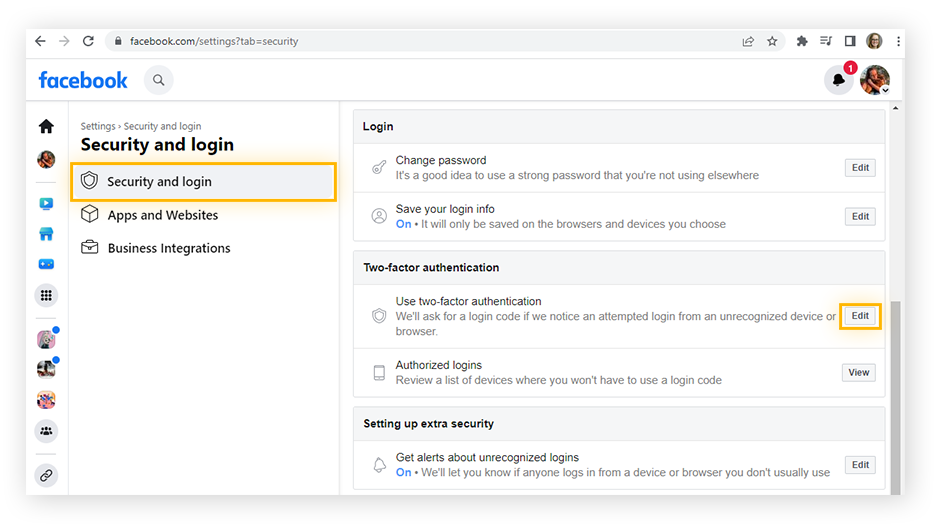
Select Security and Login in the left panel and look for Use two-factor authentication. Click Edit.
-
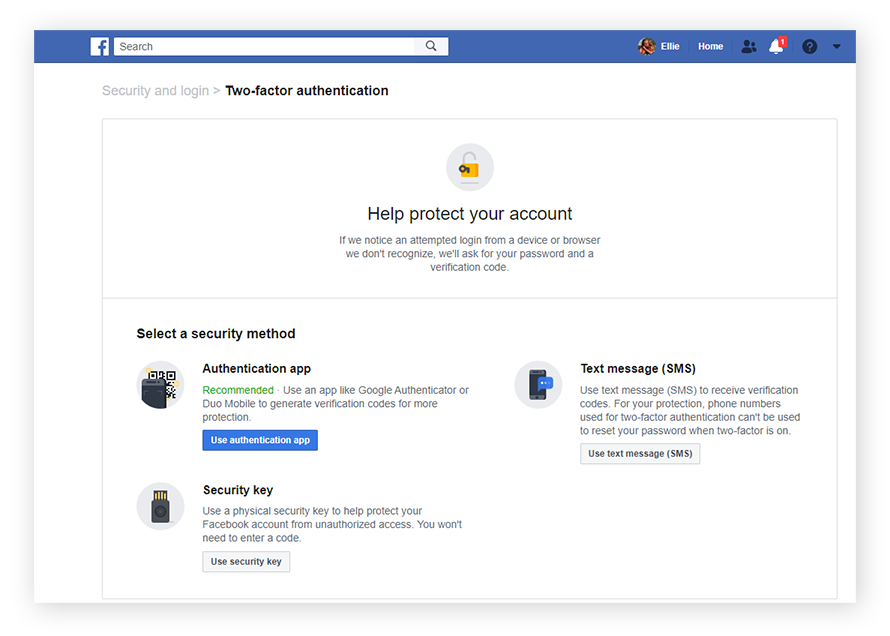
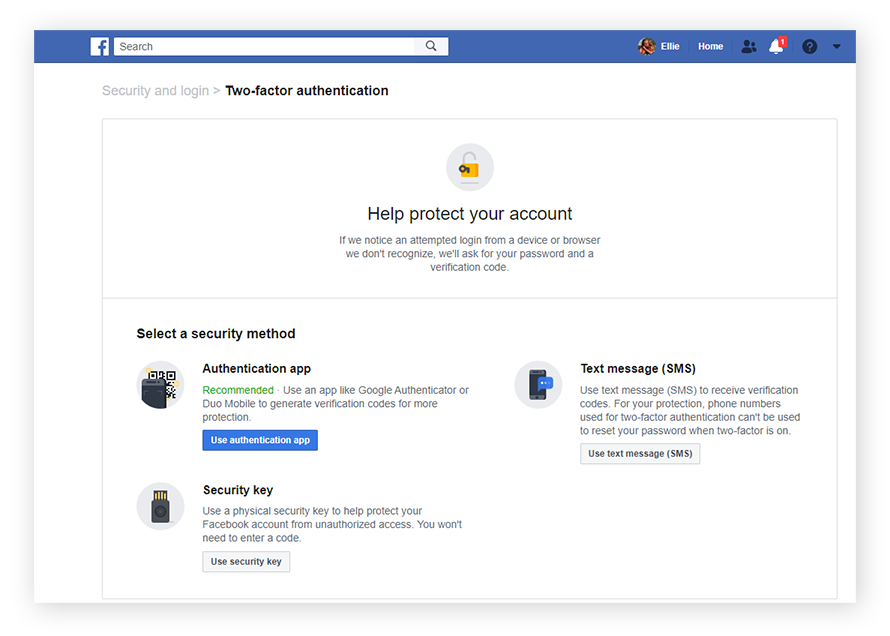
Facebook will give you options for 2FA, including an authentication app, SMS, or security key. Choose your preference.
-
If you want to use Google Authenticator and you don’t yet have it, head to Google Play or Apple’s App Store and download the app.
-
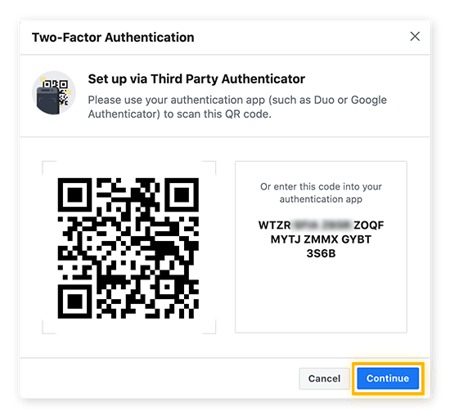
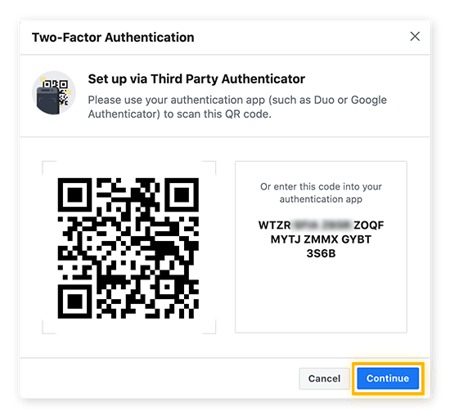
Open Google Authenticator on your phone and scan the QR code on the screen.
-
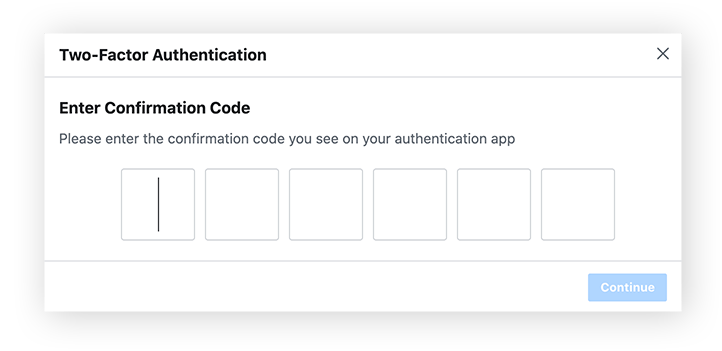
On your phone, you’ll see and confirm that you’re adding 2FA to your Facebook account. Click Continue on your computer screen.
-
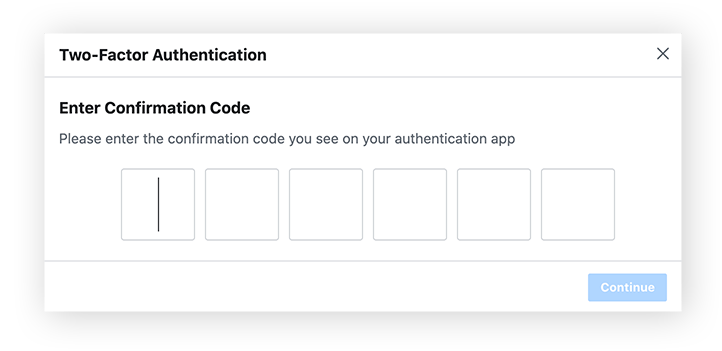
Facebook will ask that you enter a code from Google Authenticator. This code changes every few seconds so only you have access to it. Enter the six-digit number and click Continue.
-
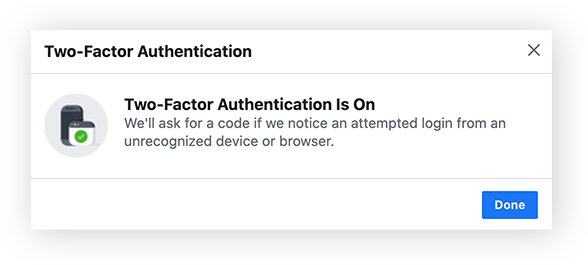
Facebook will confirm that 2FA is now turned on.
Security tip: You should enable 2FA on every account possible — especially your online banking and other sensitive accounts.
How to turn off two-factor authentication
On most accounts, you can disable two-factor authentication the same way you enabled it, usually via account security and privacy settings. On Facebook, you can turn off two-factor authentication via Security & login settings > Use two-factor authentication > Turn off. You will need to enter your password, and there will be a prompt to confirm.
You may need to do this if you get a new phone number, for example, or if it’s too inconvenient to manage at the moment. Just make sure to re-enable it when you can.
Is two-factor authentication secure?
While 2FA can add significantly more security to your online accounts, there are some flaws. For one, a lot of services don’t require 2FA when resetting a password. But for average users, 2FA is much safer than using only a password.
Another example of a 2FA flaw can be seen in the story of RSA Security. RSA Security’s entire business model rested on providing 2FA security for clients like the Pentagon — then, they were hacked. All of the tokens were leaked, turning the highest-level national security entities into easy targets to pick off.
That’s an extreme example. For regular people like you and me, 2FA is safe. Most hackers don’t target specific people, choosing instead to target high-profile or easy victims with weak security. And if one person proves hard to crack, they’ll usually move on to someone easier. For that reason, 2FA is more than enough — alongside a strong password and good security software.
When hackers do get their hands on your personal information — like passwords, social security numbers, or bank details — they often put them up for sale on the dark web. If you’ve been using the internet without 2FA, it’s a smart idea to do a dark web scan to see if any of your info has leaked.
But monitoring the dark web continuously searching for your leaked info is a fool’s errand. Thankfully, a privacy monitoring service like AVG BreachGuard can notify you automatically if your private information is leaked online. Enjoy 24/7 web monitoring, data leak notifications, and tips and advice on how to shore up your privacy and security protections with AVG BreachGuard.
Multi-factor authentication definition
Two-factor authentication is a type of multi-factor authentication (MFA). MFA refers to using two (or more) authentication factors. So every time you use 2FA, you’re also using MFA. MFA that requires more than two factors of authentication is usually used in high-security buildings, such as government facilities or other institutions holding highly classified information.
These strict-security premises may require a PIN code (something you know), an ID badge (something you have) and a fingerprint or retina scan (something you are) to grant access.
Some tech companies, banks, or other highly secure enterprises may also require three-pronged authentication to access online accounts. But most users will find 2FA sufficient for securing their personal accounts.
Have your logins already leaked?
Adding 2FA to all your online accounts will help you dramatically improve your online security. But what about all the years you’ve been accessing your personal accounts without 2FA? If your passwords have already been exposed, you may not know about it. AVG BreachGuard can help by monitoring the web for data leaks 24/7. If your personal information is ever exposed, AVG will let you know immediately, and help you take appropriate action.
Plus, you’ll get a security audit that will assess your current security protocols and offer suggestions on how to improve your passwords and tweak your settings for tighter security. In the fight against hackers, AVG BreachGuard is a crucial weapon to add to your arsenal. Start protecting your personal data today.

 Two-factor authentication requires two forms of identification to verify your account.
Two-factor authentication requires two forms of identification to verify your account.