The stunt led Fiat Chrysler Automobiles, owner of the Jeep division, to issue a formal recall of 1.4 million vehicles “to prevent the type of remote manipulation demonstrated” by the researchers.
Which parts of the Jeep were remotely controlled?
Miller and Valasek exploited the Jeep’s Internet-connected infotainment system, Uconnect, to remotely control the vehicle’s:
-
Radio
-
Digital display
-
Air conditioning
-
Windshield wipers
-
Wiper fluid
-
Transmission
-
Brakes
The last two are especially frightening. The researchers’ hack proved that, from anywhere in the world, a maliciously minded person could hop on the Internet and disable a car’s transmission, rendering it undriveable. Or its brakes, rendering it... Scrap metal.
A year later — even after Fiat Chrysler Automobiles had patched the Jeep’s remote-access flaw — Miller and Valasek managed to physically hack into the same Jeep Cherokee via a port under its dashboard. Despite needing physical access for this particular hack, the duo was able to elevate their previous attacks to life-threatening levels, including:
Bicycles are starting to look good again, aren’t they?
Is your car trying to kill you?

No, it’s not. And as long as auto manufacturers continue to take cyber threats seriously and update their software, it’s highly unlikely that anyone will take remote control of your steering wheel.
But, as with all computers, hacks are possible. And today’s cars are computers on wheels. So it’s best to be mindful of this fact. The most famous hackers in the world are certainly capable of technical feats that would astonish the everyday computer user.
“Modern motor vehicles often include new connected vehicle technologies that aim to provide benefits such as added safety features, improved fuel economy, and greater overall convenience,” the FBI says. “However, with this increased connectivity, it is important that consumers and manufacturers maintain awareness of potential cyber security threats.”
So here are a few basic steps you can take to protecting your vehicle from modern-day crooks…
6 steps to protect your car from hacks
-
Keep in touch with your car’s manufacturer
-
Update your car’s software
-
Store your keyless remote in the fridge (or faraday bag)
-
Turn off your car’s Bluetooth and Wi-Fi when not in use
-
Hide your car’s Wi-Fi password
-
Scan USB drives before plugging them into your car
1. Keep in touch with your car’s manufacturer
Give your auto manufacturer your contact information so they can reach you about software updates or vehicle recalls if necessary.
Or be proactive, and check the National Highway Traffic Safety Administration (NHTSA) recall page. Just enter your vehicle identification number (VIN) there to see if there’s been a recall for your vehicle.
 The NHTSA’s recall checker can tell you if your car has been recalled.
The NHTSA’s recall checker can tell you if your car has been recalled.
You’ll most likely find your VIN on the driver’s side of the vehicle, where the windshield and dashboard meet. If it’s not there, check the driver's side door post, or your vehicle registration card.
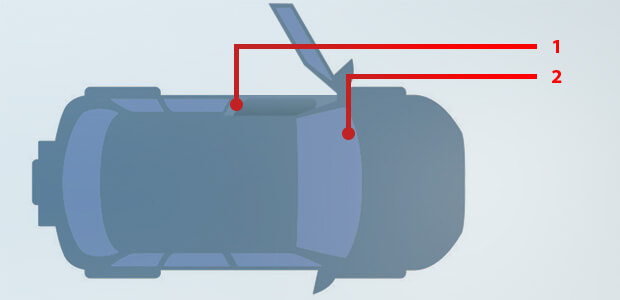 Look for your VIN on the driver’s side of the vehicle.
Look for your VIN on the driver’s side of the vehicle.
2. Update your car’s software
Outdated software can contain bugs that hackers can exploit to steal your private data or take control of your car. So just as you’d check your computer for software updates, be sure to keep an eye out for notices from your auto manufacturer, and bring your car in for updates as soon as they’re available.
3. Store your keyless fob in the fridge
Or get a faraday bag. Why? Because in a matter of seconds, thieves can break into your car by amplifying the signal from your keyless remote and tricking the car into thinking you’re nearby. Here’s a video of that in action:
What dark arts make this possible? Well, if your car has keyless entry, when you try the door handle, the car will send a wireless signal to your keyless fob. If your keyless fob is nearby, it will respond, and your car door will unlock. If the fob is more than a few feet away, it won’t be able to respond, and the door won’t open.
But here’s the thing… If a hacker knows where your keys are (e.g., often kept by the front door), he could stand outside your home, hold a device near your door to amplify your keyless fob’s range, and allow an accomplice to open your car door.
But if your keyless fob is in a faraday bag (or your refrigerator), then its signal will be blocked, preventing criminals from hacking open your car doors.
4. Turn off your car’s Bluetooth and Wi-Fi when not in use
An open wireless connection could allow criminals to walk up to an unpatched car, connect to its entertainment system, and take control of one or more parts of the vehicle.
The FBI warns, “Vulnerabilities may exist within a vehicle’s wireless communication functions, within a mobile device – such as a cellular phone or tablet connected to the vehicle via USB, Bluetooth, or Wi-Fi – or within a third-party device connected through a vehicle diagnostic port. In these cases, it may be possible for an attacker to remotely exploit these vulnerabilities and gain access to the vehicle’s controller network or to data stored on the vehicle.”
So if you’re not using your car’s Bluetooth or Wi-Fi, it’s best to switch them off.
5. Hide your car’s Wi-Fi password
This one’s simple. If your car has its own Wi-Fi, be sure to keep the password hidden. Leaving it in your glovebox could expose you to attack if your car is ever broken into.
6. Scan USB drives before plugging them into your car
An infected USB drive could contain malicious code designed to compromise your car. So be sure to scan any USB drive before plugging it into your car.
AVG AntiVirus FREE includes USB scanning in its Other Scans menu. Just plug your USB drive into your computer and run the USB/DVD Scan to see if it’s safe to use in your car.
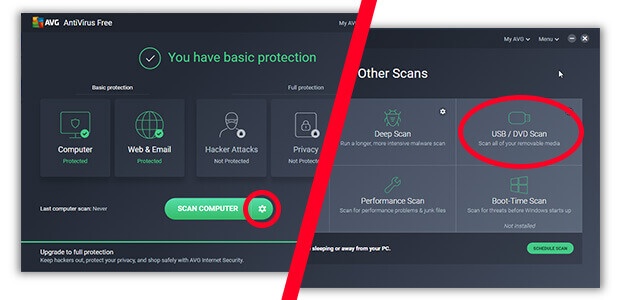 To scan a USB drive, click the gear icon and then USB/DVD Scan.
To scan a USB drive, click the gear icon and then USB/DVD Scan.
What should you do if you think your car’s been hacked?
If you think someone has hacked (or tried to hack) your car, the FBI recommends you follow all 4 of these steps.
1. Check for vehicle recalls or software updates
See if there have been any recalls for your vehicle, and check your auto manufacturer’s website for potential software updates for your vehicle.
2. Contact your auto manufacturer or authorized dealer
Explain your concerns, and they may be able to help you out.
3. Contact the National Highway Traffic Safety Administration
File a vehicle safety complaint with the NHTSA. (As the regulatory agency for setting and enforcing federal motor vehicle safety standards in the United States, the NHTSA also works to improve automobile safety from a cybersecurity perspective.)
4. Contact the FBI
Inform your local FBI field office of your concerns, and also file a complaint with their Internet Crime Complaint Center (IC3).
In summary… Don’t panic
As I’ve said, car hacks are possible, but not very likely. Of course, this may change as more cars become connected to the Internet. (Forbes reports that 152 million connected cars will be sold globally by the year 2020.)
But for the time being, just be aware of the risks, keep your car’s software updated, and report any suspicious vehicle behavior to your auto manufacturer and the authorities the moment it happens.


 The NHTSA’s recall checker can tell you if your car has been recalled.
The NHTSA’s recall checker can tell you if your car has been recalled.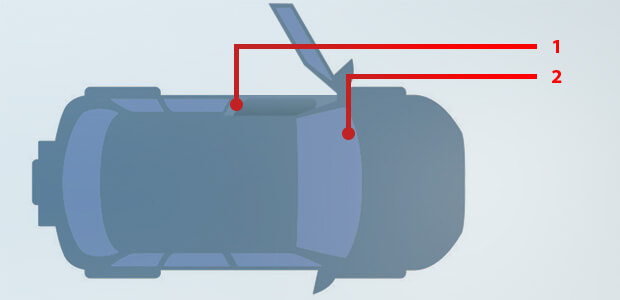 Look for your VIN on the driver’s side of the vehicle.
Look for your VIN on the driver’s side of the vehicle.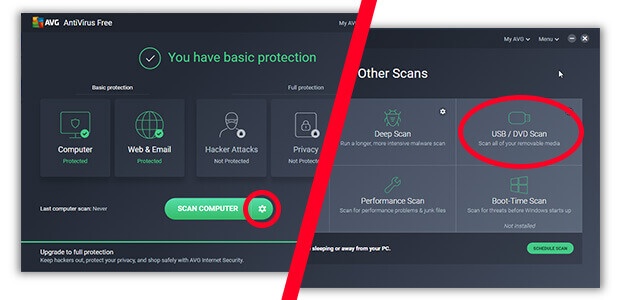 To scan a USB drive, click the gear icon and then USB/DVD Scan.
To scan a USB drive, click the gear icon and then USB/DVD Scan.




