Twitter: the obnoxious tourist of social networks. Loud, opinionated, and may give you something if you don’t use protection. Here are thirty-three tweetable Twitter tips to protect your safety and privacy, clocking at 280 characters or less. #tweetsafely
Twitter safety for basics
1. OK LISTEN this is important. It’s all fun and games until someone gets hacked. Breaking into your Twitter account doesn’t take much, but you can turn yours into a fortress by following these simple security tips. We’ll go from super basic to more advanced.
2. Twitter privacy is binary: your tweets are either all private (which means only your followers can see them), or totally public (which means everybody can). There’s no picking and mixing depending on the post, unlike on Facebook. It’s either/or, and it’s up to you to decide.
.gif?width=400&name=200w-d%20(1).gif)
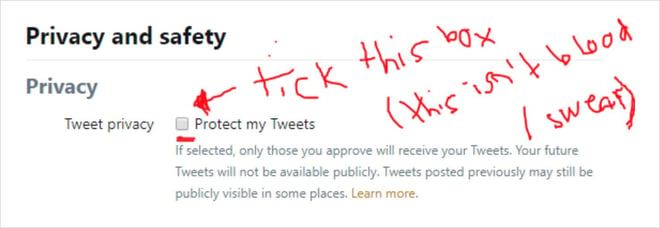
3. Here’s how to to make your tweets private on the Twitter desktop site: 1) click on your pic in the upper right menu 2) go to Settings and privacy 3) click on Privacy and safety on left menu 4) Tick the box next to Protect your Tweets.
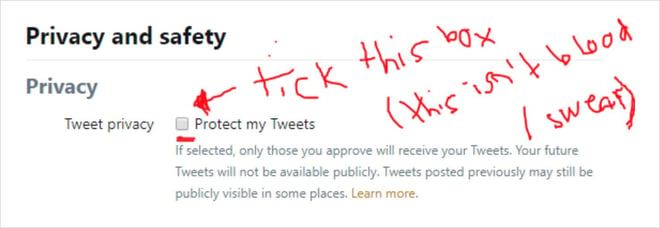
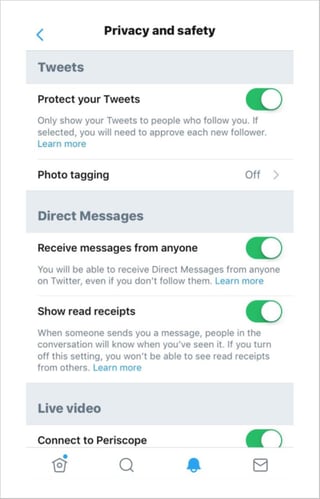
4. To make Twitter private on iOS for iPhone and iPad: 1) tap your profile pic in the top menu 2) tap Settings and privacy 3) tap Privacy and safety 4) move the Protect your Tweets toggle to green.
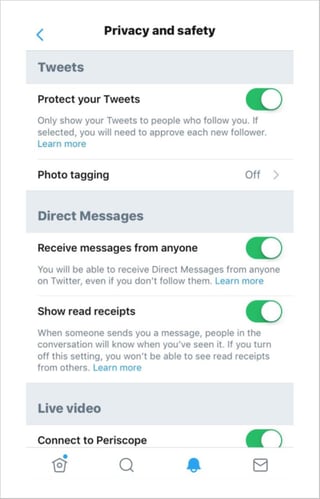
5. To make your Twitter private on Android, 1) tap your profile pic in the top menu (or the navigation menu icon — it looks like a sideways sandwich) 2) tap Settings and privacy 3) tap Privacy and safety 4) check the box next to Protect your Tweets.
6. When you set your Twitter as private, it works for all your tweets — past, present and future. BUT (yes there’s a but) some of your previously public tweets may still be found if they’re indexed by search engines, third-party apps etc.
7. That’s the basics done. And now let’s talk about GEOTAGGING — the new security craze for the fanciest of Twitter users.
.gif?width=400&name=200w-d%20(2).gif)
Geotagging. All the cool kids are doing it. (But don’t.)
8. Whenever you take a pic with your smartphone, it’s automatically loaded with tons of potentially compromising info, like the GPS coordinates of the place the pic was taken (yep). This is called the EXIF data file, and nearly all smartphones add it to your pics.
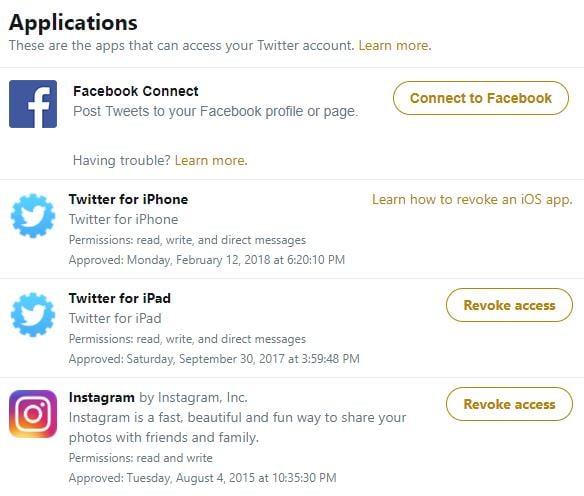
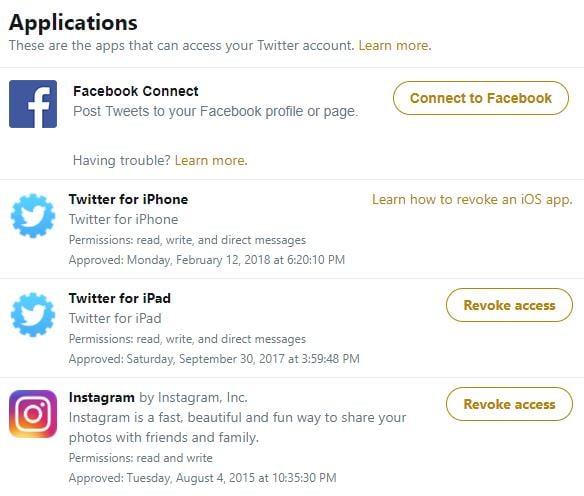
9. Looking at the exact geographical coordinates of that pic you just took and uploaded to social media is a great way for stalkers to know where you are, and house robbers to know where you’re not. Especially since the EXIF file also contains the time the pic was taken.
10. Twitter says it strips the EXIF data of your pics before posting them, so that’s good — but wait! Twitter looks at the EXIF data to show you suggested locations, and while those may not be as precise as GPS coordinates, they’re still pretty sketchy in the wrong hands
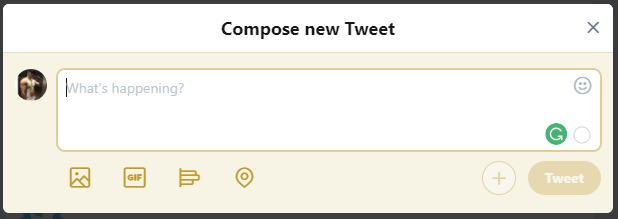
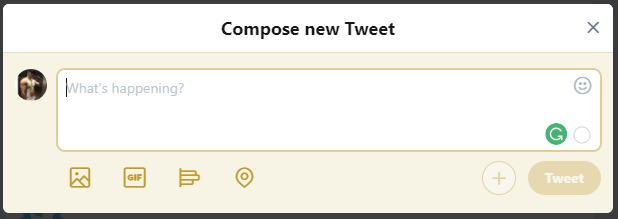
11. To hide your location, head to twitter.com and open the Compose new Tweet box. Click on the location button (looks like a pin). Choose Remove location from the drop-down menu. This removes location info from your future tweets too.
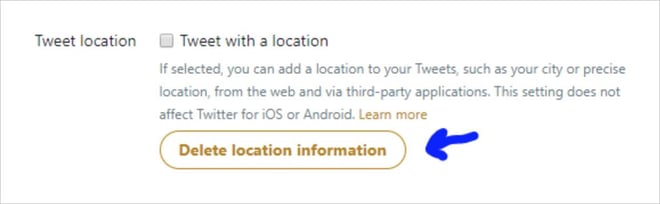
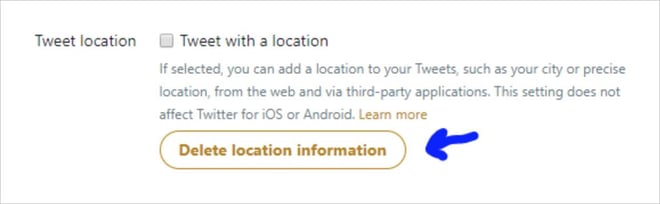
12. You can also remove location info from all your previous tweets. 1) On twitter.com, click on your profile pic to open the menu. 2) Click on Settings and privacy. 3) Click on Privacy and safety. 4) Under Tweet location, click on Delete location information
Careful with third-party apps
13. Quizzes, games… Spammy or unsafe apps can accumulate in the backend of your Twitter. Get rid of any third-party apps you don’t use, recognize and/or trust: head to the Apps tab in your account settings and hit Revoke access next to anything you don’t explicitly want
Short URLs can be dangerous, so preview them
14. Short URLs (bit.ly, goo.gl, tinyurl, etc) were a lifesaver back in the days of 140 character limits. Today Twitter trims every URL to 23 characters max (and gives you 280 characters to fill per tweet) so compressing URLs isn’t nearly as important
15. Still, old habits die hard and every character counts, so shortened URLs remain common. But they’re actually problematic af. Because they are meaningless and generic, you have no idea where they’re taking you until you get there. And ‘there’ can be a bad, bad place
.gif?width=400&name=200w-d%20(3).gif)
16. In fact, cyber criminals loooooove shortened URLs for this very reason. Tricking people into clicking these links on social media is an increasingly popular method for spreading virus, trojans and other malware. Click, download, doom
17. You can protect yourself by using one of several services that expand short links for you before you open them, like CheckShortURL. Or one of the many free browser-based link scanners like Scanurl, which checks URLs for malware regardless of length
18. You can make things even simpler for yourself by installing a browser extension to check your short URLS. For Chrome, consider LinkPeelr. For Firefox, you could try PageExpand. URLxray is a ‘bookmarklet’ for Internet Explorer
19. And having a good, updated antivirus installed in your PC and mobile will save you a load of trouble, should you ever click on a dodgy link. Here’s an excellent one — and it's 100% free
Beware of Twitter scams
20. Phishing scams are sliding into your DMs. Flirty strangers, hacked accounts, pay-for-followerz schemes… You get a direct message or tweet with a link, which takes you to a fake site that asks you to enter login details, personal info and/or credit card details
21. Some of these phishing sites look just like the real thing. There have been cases of phishing scams distributed not through DMs or tweets, but through malicious Twitter ads. Never click on DM links, even if they come from friends’ accounts. Hacks happen — often
Help! Someone hacked my Twitter
22. Did someone break into your Twitter account? There are two possibilities: 1) You’re a celebrity in full damage-control mode because your racist tweet lost you a movie franchise deal; or 2) Somebody broke into your Twitter account
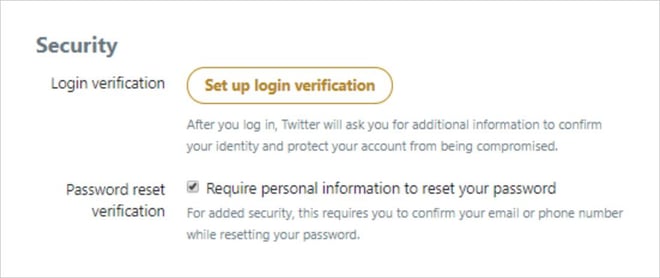
23. There are two things you can do to help PREVENT someone from breaking into your account (or as people refer to it, ‘hacking into’ your Twitter): 1) set up login verification, and 2) set up extra password reset verification
24. Login verification is an extra login step: apart from your usual password, you’ll be send a one-off code to your phone via SMS and use it to get into your account. This makes it much harder for anyone else to get in — they would need to have your password AND your phone
25. To set up login verification: 1) Click your profile icon 2) Go to Settings and privacy 3) Open Account settings 4) Click on Set up login verification. Follow the onscreen instructions (enter your password, click Verify, wait for your SMS code, enter it, that’s pretty much it)
26. If you don’t want to/can’t use your phone number for verification, there are a number of Twitter-compatible authenticator apps you can use (like Google Authenticator). This is a bit click-intensive, so best to follow these steps to set it up.
27. Do you keep getting password reset emails or text messages from Twitter which you didn’t request? Does it mean someone is trying to break into your account? Could be someone with a similar email or username trying to reset their password. Could be your ex. Who knows.
28. To be on the safe(r) side, go to twitter.com, head to Account, and in the Security section, tick the box that says Require personal information to reset your password. This helps secure your password against malicious or accidental resets
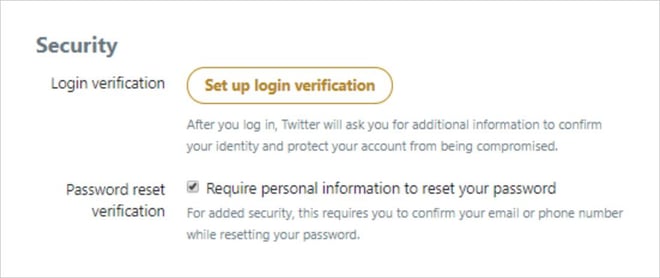
29. If your account’s ALREADY HACKED, do this. If you can login, request a new password right away. Once you log in with your new password, remove all third-party apps you don’t recognize and trust under the Apps tab. Scan your device for malware afterwards to be safe.
30. If you cannot login to your Twitter account, request a new password. If you can log in with your new password, check it for odd tweets or follows, and remove untrusted apps. If you still can’t login, send Twitter a support request and select Hacked account
Help! Someone’s impersonating me on Twitter
31. Is someone pretending to be you on Twitter? While nobody will ever quite match your online wit, it doesn’t take much to create a fake profile with a publicly available photo of you, your name and a reasonably similar username. Here’s how you fight back
32. You have two ways of reporting a Twitter impersonator. This is one: Go to this link and select the options that apply to you. They’ll ask you to enter a few details and upload a copy of your government-issued photo ID. Click Submit, and Twitter will take care of the rest
33. You can also report an impersonator directly from their fake profile: 1) Click on the three-dot icon (if on Android or desktop) or the gear icon (if you’re on iOS) next to the profile’s Follow button. 2) Select Report, then They’re pretending to be me or someone else.

.gif?width=400&name=200w-d%20(1).gif)
.gif?width=400&name=200w-d%20(2).gif)
.gif?width=400&name=200w-d%20(3).gif)